Category:I802 Firewalls and VPN IPSec
Firewalls and VPN/IPSec
General information
ECTS: 4
Lecturer: Lauri Võsandi
Scenario
In this course we will attempt to set up a network similar to a corporate network with multiple offices, eg http://docplayer.it/docs-images/20/596222/images/25-0.png
We will use VPN software to connect subnets to each other and we will use VPN software to connect our personal computers to the intranet.
Setting up virtual machine hosts
For this course we have 3 Sun servers, each with 16GB of RAM. In each server we should be able to create 3 or more virtual machines. As host operating system we will install Ubuntu 16.04 server. On disks set up ext4 on mdraid set up in RAID1 configuration.
For virtualization let's use libvirtd and virt-manager on your Ubuntu laptops, for Windows and Mac unfortunately there is no decent UI available instead installing web interface such as Kimchi is recommended.
To install libvirtd on the server:
apt install libvirtd-bin qemu-kvm
Also add the primary user to the libvirtd group:
sudo gpasswd -a $USER libvirtd
On your laptop first set up SSH keys between the laptop and server with ssh-keygen and ssh-copy-id. And then you can install virt-manager with:
sudo apt install virt-manager
Copy CD ISO files into /var/lib/libvirtd/images using scp or FileZilla.
Continue with creating a virtual machine for each service. For Windows 2012 server virtual machines use 2G of RAM and 50G of storage. For Ubuntu 16.04 server installations use 1G of memory and 50G storage. For Ubuntu 16.04 MATE desktop installations use 2G of RAM.
In order to set up virtual switch inside the server use Linux's built-in bridges, start with installing bridge-utils:
apt install bridge-utils
Reconfigure your server's /etc/network/interfaces, replace X with number relevant to your server. Also replace eth0, eth1 and eth2 with the network interfaces available in your machine:
# The loopback network interface auto lo iface lo inet loopback # Wide area network interface auto br-wan iface br-wan inet dhcp # Until we set up router in a VM we will use DHCP so we can have internet access in 417 bridge_ports eth0 # Local area network interface auto br-lan iface br-lan inet static address 172.16.X.1 netmask 255.255.255.0 bridge_ports eth1 # Management interface auto eth2 iface eth2 static address 192.168.12.1X netmask 255.255.255.0
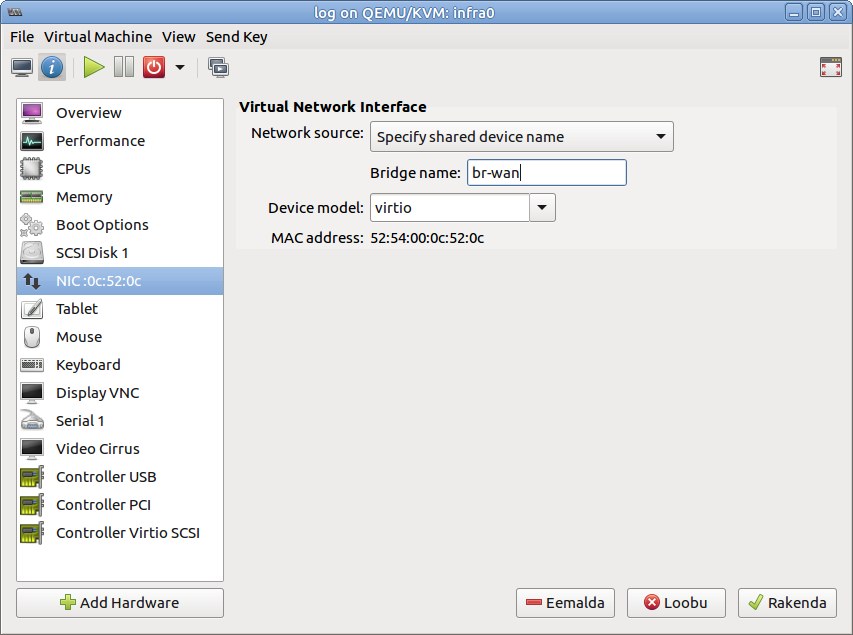
When creating virtual machines, configure network as shown in the screenshot below:
This way your VM-s should be able to access the Internet as the physical machine can
Setting up router
On Wednesday 14. September we will configure OpenWrt as a router in a virtual machine. Download the OpenWrt image and uncompress it:
cd /var/lib/libvirt/images/ wget https://downloads.openwrt.org/chaos_calmer/15.05.1/x86/kvm_guest/openwrt-15.05.1-x86-kvm_guest-combined-ext4.img.gz gunzip openwrt-15.05.1-x86-kvm_guest-combined-ext4.img.gz
Add second network interface to your router's VM. Configure first NIC as connected to br-wan and second one connected to br-lan.
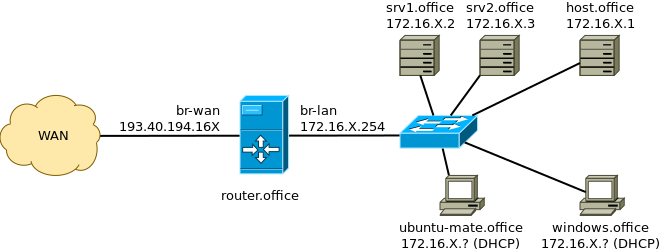
After that you should end up with topology similar to this:
To clarify: 'srv1.office' and 'srv2.office' are the Ubuntu 16.04 servers, you should have configured static IP addresses or set a static lease from the router. The 'router.office' refers to the OpenWrt router you just set up. The router serves IP addresses using DHCP to 'ubuntu-mate.office' Ubuntu MATE 16.04 workstation and 'windows.office' refers to Windows workstation. Your physical server 'host.office' can be accessed as well. The 'office' throughout the diagram refers to your domain name, use abbrevations such as hq, rnd, devops for that.
Offices
Headquarters
Gateway: 193.40.194.220
DNS: 193.40.0.12, 193.40.56.245
Public IP address (eth0): 193.40.194.160/24
Internal IP address of the physical server (eth1): 172.16.1.1/24
Management network IP address (eth2), accessible from robotics club: 192.168.12.10
Team members: Keijo, Anton, Mohanad, Etienne
Services:
- BIND9 as public DNS server, also figure out what domain name we should/can use
- domain controller, at this point primarily for user accounts (Keijo)
- nginx web server, for company's homepage (Anton)
- SMB/CIFS fileserver, join to domain (Etienne)
- VPN server for other subnets, presumably OpenVPN
Research & development
Gateway: 193.40.194.220
DNS: 193.40.0.12, 193.40.56.245
Public IP address (eth0): 193.40.194.161/24
Internal IP address of the physical server (eth1): 172.16.2.1/24
Management network IP address (eth2), accessible from robotics club: 192.168.12.11
Team members: Marvin, Madis, Taavi, Berit, Joosep
Services:
- Git hosting, for sharing scripts, set up LDAP to authenticate with domain controller
- Wiki, for exchanging information, set up LDAP to authenticate with domain controller and later possibly configure web server to authenticate with Kerberos
- Windows XP workstation, join to domain
- Ubuntu 16.04 MATE workstation, join to domain. Possibly also set up as LTSP server, so we can boot terminals in 417
- OpenVPN connection to headquarters, use shared secret at first, later X509 certificates
- Pastebin, possibly later implement Kerberos support (Berit)
Devops
Gateway: 193.40.194.220
DNS: 193.40.0.12, 193.40.56.245
Public IP address (eth0): 193.40.194.162/24
Internal IP address of the physical server (eth1): 172.16.3.1/24
Management network IP address (eth2), accessible from robotics club: 192.168.12.12
Team members: Arti, Meelis Hass, Artur O, Sheela, Ilja (exchange)
Services:
- IRC, for chatting
- Certificate management for roadwarriors
- Monitoring software of your choice to make sure that services are up and running, possibly use LDAP for authentication
- E-mail for sending notifications from monitoring software at first
- Later, in the beginning just monitor public services: OpenVPN connection to headquarters
Pentest
Find security issues in the deployed services.
Team members: Kustas, Ender, Indrek (?)
This category currently contains no pages or media.