Radare2
Radare [1] is an open source and multi-platform framework for Reverse Engineering activities which supports assembly and disassembly many architectures and binary formats [2]. As any other reversing framework, Radare framework aims to recognize high level features on machine code, such as: data structures, functions and execution flows. Radare has buildings for the most populars Operating Systems, such as: Microsoft Windows, Mac OS X, Linux, BSD, iPhone OS, Solaris and MeeGo. Radare offers few options of interactive graphical interfaces, such as: Web, GTK (Python) and ASCII-Art graph. Another very useful characteristic due to its designing is the capacity to easily implement new architectures, binary formats and analyses [3][4]. Radare provides an open API and with many bindings for many programming languages, such as: Python, Java, Ruby, Go and Perl. Radare is also integrated with the most popular debuggers supporting local and remote debugging [5], such as: gdb, rap, webui, r2pipe, winedbg and windbg.
The framework is essentially composed by 7 executables:
Radare2 It is the core of of the hexadecimal editor and debugger. It allows you to open a number of input/output sources as if they were simple, plain files, including disks, network connections, kernel drivers, processes under debugging, and so on.
Radare2 implements an advanced command line interface for moving around a file, analyzing data, disassembling, binary patching, data comparison, searching, replacing, visualizing. It can be scripted with a variety of languages, including Ruby, Python, Lua, and Perl.
Rabin2 It allows you to extract information from executable binaries, such as ELF, PE, Java CLASS, and Mach-O. rabin2 is used by the core to get exported symbols, imports, file information, cross references (xrefs), library dependencies, sections, etc.
Rasm2 It is a command line assembler and disassembler for multiple architectures (including Intel x86 and x86-64, MIPS, ARM, PowerPC, Java, and MSIL).
Rahash2 An implementation of a block-based hash tool. From small text strings to large disks, rahash2 supports multiple algorithms, including MD4, MD5, CRC16, CRC32, SHA1, SHA256, SHA384, SHA512, par, xor, xorpair, mod255, hamdist, or entropy. rahash2 can be used to check the integrity of, or track changes to, big files, memory dumps, and disks.
Radiff2 It is a binary diffing utility that implements multiple algorithms. It supports byte-level or delta diffing for binary files, and code-analysis diffing to find changes in basic code blocks obtained from the radare code analysis, or from the IDA analysis using the rsc idc2rdb script.
Rafind2 It is a program that allows you to find byte patterns in files.
Ragg2 A frontend for r_egg. ragg2 compiles programs written in a simple high-level language into tiny binaries for x86, x86-64, and ARM.
Rarun2 A launcher for running programs within different environments, with different arguments, permissions, directories, and overridden default file descriptors.
Rarun2 is useful for:
Crackmes Fuzzing Test suites
Rax2
A minimalistic mathematical expression evaluator for the shell that is useful for making base conversions between floating point values, hexadecimal representations, hexpair strings to ASCII, octal to integer, etc. It also supports endianness settings and can be used as an interactive shell if no arguments are given.
Getting radare2
You can get radare from the website, http://radare.org/, or the GitHub repository, https://github.com/radare/radare2.
Binary packages are available for a number of operating systems (Ubuntu, Maemo, Gentoo, Windows, iPhone, and so on). Yet, you are highly encouraged to get the source and compile it yourself to better understand the dependencies, to make examples more accessible and of course to have the most recent version.
A new stable release is typically published every month. Nightly tarballs are sometimes available at http://bin.rada.re/.
The radare development repository is often more stable than the 'stable' releases. To obtain the latest version:
$ git clone https://github.com/radare/radare2.git
Install
The easiest way to install radare2 from git is by running the following command:
$ sys/install.sh
If you want to install radare2 in the home directory without using root privileges and sudo, simply run:
--itaal (talk) 03:17, 25 August 2016 (EEST)$ sys/user.sh
Basic Radare Usage
To be allowed to write files, specify the -w option to radare when opening a file. The w command can be used to write strings, hexpairs (x subcommand), or even assembly opcodes (a subcommand). Examples:
> w hello world ; string > wx 90 90 90 90 ; hexpairs > wa jmp 0x8048140 ; assemble > wf inline.bin ; write contents of file
Appending a ? to a command will show its help message, for example, p?.
To enter visual mode, press V<enter>. Use q to quit visual mode and return to the prompt. In visual mode you can use HJKL keys to navigate (left, down, up, and right, respectively). You can use these keys in cursor mode toggled by c key. To select a byte range in cursor mode, hold down SHIFT key, and press navigation keys HJKL to mark your selection. While in visual mode, you can also overwrite bytes by pressing i. You can press TAB to switch between the hex (middle) and string (right) columns. Pressing q inside the hex panel returns you to visual mode.
Basic Visual Debugger Session
Radare is mostly command line usage debugger with additional possibility to use the most awesome visual memory representation to date. Makes you feel 1337 real fast. A simpler method to use debugger in radare is to switch it to visual mode. That way you will not have to remember many commands nor to keep program state in your mind. To enter visual mode use V:
[0xB7F0C8C0]> V
The initial view after entering visual mode is a hexdump view of current target program counter (e.g., EIP for x86). Pressing p will allow you to cycle through the rest of visual mode views. You can press p and P to rotate through the most commonly used print modes. Use F7 or s to step into and F8 or S to step over current instruction. With the c key you can toggle the cursor mode to mark a byte range selection (for example, to later overwrite them with nop). You can set breakpoints with F2 key.
In visual mode you can enter regular radare commands by prepending them with :. For example, to dump a one block of memory contents at ESI: x @ esi
To get help on visual mode, press ?. To scroll help screen, use arrows. To exit help view, press q.
A frequently used command is dr, to read or write values of target's general purpose registers. You can also manipulate the hardware and extended/floating point registers.
Challenge
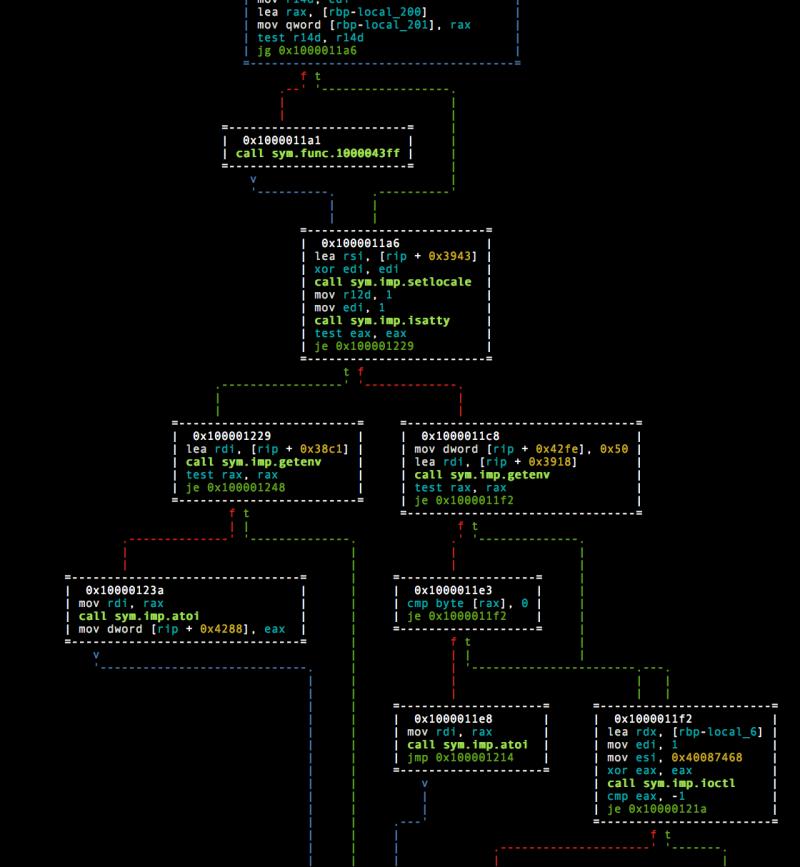
Use Radare2 to find out this programs function and crack it.
https://1drv.ms/u/s!APP7wJujw7BWrR0
Information to find out: -Endian info -Interpeter -Arhitecture -What system calls are made ? Finally, crack the executable.
Hints:
PEheader
r2 automated analysis
r2 visual modes
References
[1] http://rada.re/r/ [2] https://en.wikipedia.org/wiki/Radare2#Supported_architectures.2Fformats [3] https://github.com/radare/radare2/wiki/Implementing-a-new-architecture [4] https://github.com/radare/radare2/wiki/Implementing-a-new-analysis-plugin [5] http://solidsec.blogspot.de/2015/09/reversing-elf-binaries-remote-debugging.html