Local Attacks: Difference between revisions
mNo edit summary |
|||
| (97 intermediate revisions by one other user not shown) | |||
| Line 1: | Line 1: | ||
= | = Abstract = | ||
This article will be concerned about one of the common hacking methods in recent decades or even nowadays it is still being used by attackers. Its named Local Attack, this name is not the international official name for it. It was called by many Vietnamese Hackers, by somehow I realized it's quite good to describe partly of this attack method, so I'd like to take this name to be " our speaking" at least in this article. "This name is not available in google if you type by English " | |||
I will illustrate the definition of Local Attack as well as the difficulties we will be suffered when we apply it beside its powerful. I will be talking detail step by step belongs with the certain knowledge what we need to know basically to do much straightforwardly and more understand its purpose. The knowledge requirement will be not hard to stop you getting the most powerful of hacking such as Web App, Linux command lines, Networking, etc. | |||
Because of the security of our website and server, I will not show the php shell link in this article. I apologize for this inconvenient. | |||
Keywords : ''Hacking, Local attack ,Linux , Web App.'' | |||
[['''''!!! This article is served for education purpose only, I will not responsibility for any harm made by other ones !!!''''']] | |||
= Local Attack Introduction= | |||
==What is Local Attack?== | ==What is Local Attack?== | ||
In generally, once we host the website to server, after that the user will be provided an " user account" and the directory/folder to mange their website. For instance, the user | In generally, once we host the website to server, after that the user will be provided an " user account" and the directory/folder to mange their website. For instance, the first user has a website "A" and one directory/folder : /home/user1 to manage first user Similarly, the second user has a website "B" and one directory/folder /home/user2 to manage. | ||
Local attack is | Local attack is the method which is applied to hack a website in the same server. For example, I want to attack website "A" from user 1, but unfortunately I could not find out the vulnerabilities to exploit and get an lien from it that means I have no way to attack based on this site "A". So, I will look for the websites which are being on the same server with "A", could be website "B" or "C". | ||
Based on site "B" or "C" | Based on site "B" or "C" both of them are getting some vulnerabilities or another words is " hackable ". After getting the authorities on these site "B" or "C", I will upload the php file named " Shell " to the server of "B" or "C" it's also the server of website "A". The hacking process is starting from now..... | ||
[[File:Local1.png]] | [[File:Local1.png]] | ||
''Firgure 1: Php shell was uploaded to host of the website.'' | |||
==Pros and Cons of Local Attack== | ==Pros and Cons of Local Attack== | ||
'''Pros:''' | '''Pros:''' | ||
* | *Does not take a lot of time. | ||
* | *Easy to interact with the server via shell and exploit it. | ||
'''Cons:''' | '''Cons:''' | ||
*The administrator | *Leave the " mark ", The administrator would be able to find where the shell comes from. | ||
*Local | *If the websites are using separate server, Local Attack will be gotten some certain difficult. | ||
=What we need to know?= | =What we need to know?= | ||
==Host and Shared-Host== | ==Host and Shared-Host== | ||
Normally for web site, its data must be stored on one server (server) is always active and connected to the internet. Storage space on the server used to store the data of the website is called the host. For a number of agencies and organizations, the hired one server for data storage is not practical website. Due to their needs is simply stored, further 1 server rental price is not cheap. Therefore, shared hosting is a reasonable choice. With shared hosting, server memory space is divided into many small hosts, and are separate from each rental. So on one server will contain data for multiple websites, and there is also a source of security for developing local attack. | Normally for web site, its data must be stored on one server (server) is always active and connected to the internet. Storage space on the server used to store the data of the website is called the host. For a number of agencies and organizations, the hired one server for data storage is not practical website. Due to their needs is simply stored, further 1 server rental price is not cheap. Therefore, shared hosting is a reasonable choice. With shared hosting, server memory space is divided into many small hosts, and are separate from each rental. So on one server will contain data for multiple websites, and there is also a source of security for developing local attack. | ||
==Decentralized system== | ==Operating System and Decentralized system== | ||
'''Unlike Windows, Linux operating system has a decentralized system is complicated and strict. Linux supports three | |||
The Operating system of the server must be Linux | |||
'''Unlike Windows, Linux operating system has a decentralized system is complicated and strict. Linux supports three permissions to do with files :''' | |||
| Line 48: | Line 66: | ||
''You can read more here: http://linuxcommand.org/lts0070.php'' | |||
==Shell== | ==Shell== | ||
| Line 71: | Line 77: | ||
In this tutorial, I will use the shell php named: '''Shell r57 or c99'''. You can download it on google | In this tutorial, I will use the shell php named: '''Shell r57 or c99'''. You can download it on google | ||
''*I recommend you use those shells in virtual machines | See more here: | ||
-http://linuxcommand.org/lts0010.php | |||
-http://linuxcommand.org/learning_the_shell.php | |||
''*I recommend you use those shells or download it in virtual machines .'' | |||
=How to Local attack step by step ?= | =How to do Local attack step by step ?= | ||
1. View the list of user in server | 1. View the list of user in server | ||
| Line 91: | Line 103: | ||
The command line to get the user: | The command line to get the user: | ||
cat /etc/passwd | |||
Some cases, If the above command line does not show the user list, we could try this: | Some cases, If the above command line does not show the user list, we could try this: | ||
ls -l /home/ | ls -l /home/ | ||
If the server ban to cat the passwd, use could use these command lines: | If the server ban to cat the passwd, use could use these command lines: | ||
less /etc/passwd | |||
./cat/etc/passwd | ./cat/etc/passwd | ||
==Find the path file config.php== | ==Find the path file config.php== | ||
| Line 112: | Line 121: | ||
-With linux: | -With linux: | ||
/home/user/public_html | /home/user/public_html | ||
Or other | |||
-Joomla: | -Joomla: | ||
| Line 126: | Line 131: | ||
path/wp-config.php | path/wp-config.php | ||
- | This is the default path of those type of servers it's being used. It might be changed depended on Administrators (This is mainly due to the habits of programmers ). | ||
(To search for the source path, search by keywords: "cwd", we will see similar code: "require_once (CWD. '/includes/init.php');" - This is the path defaults resulting init.php file)) ...... | |||
==Get the information from config file== | |||
''This is the most difficult step of the method'' | |||
===The basic command lines using for Local Attack=== | |||
-ls, dir: List the names of the files inside the folder | |||
ls -al, ls -lia: List the names and attributes of files inside the folder | |||
ls -lia "/home/lphanvan/public_html/@ender/includes.config.php" | |||
-sand, ./cat, less, more, tail: View contents inside the file: | |||
cat "/home/lphanvan/public_html/@ender/includes/config.php" | |||
- | -ln: Command symbolic link: | ||
ln -s "/home/lphanvan/public_html/@ender/includes/config.php%20ender.ini" | |||
- | -cd: Convert directory | ||
For example, to navigate to the folder | |||
cd / home / lphanvan/ public_html / @ender/ includes / itcollege | |||
cd ~: Go to Facebook's home directory | |||
-chmod: Distribution rights for files or folders: | |||
chmod 400 config.php (working in the directory where the file includes config.php) | |||
-mkdir: create directory: | |||
For me, I want to create a folder in the directory includes: | |||
mkdir / home / lphanvan/ public_html / @ ender/ includes / itcollege | |||
-touch: Create file: | |||
touch /home/lphanvan/public_html/@ender/includes/itcollege.php | |||
-tar, tip: compress and uncompress command: often used in root symlink | |||
- | tar -zcvf enderhacked.tar.gz soleil (Compressed file folder enderhacked.tar.gz ender) | ||
tar -zxvf enderhacked.tar.gz (unzip files enderhacked.tar.gz) | |||
See more here: http://linuxcommand.org/lts0070.php | |||
===Some techniques to get useful information from config.php=== | |||
- | 1-Using the cat command, dim to see the folder name, file and read the file contents. | ||
Example: dir / home / lphanvan/ public_html / includes | |||
cat /homme/lphanvan/public_html/includes/config.php | |||
But now the majority of servers are not allowed to exercise this function should apply this method will not work, | |||
2-Using Symbolic links - Referred to as symlink | |||
Symbolic links are basic techniques, and almost as important that the majority of the first attaker think before doing work local attack. | |||
ln -s "/ home / lphanvan/ public_html / @ ender/ includes /config.php% itcollege.ini " | |||
It can be understood simply create one file on the host itcollege.ini with identical content lphanvan config.php file on the server with the user's path | |||
"/home/lphanvan/public_html/@ender/includes/config.php" | |||
''You can read more detail here: http://linuxcommand.org/learning_the_shell.php'' | |||
==Cracking and Changing the admin's password !!!!== | |||
In this case the admin's password does not be encoded by hash, so you do not need to crack it. In many cases, the content would not be showed and the password will be in hash. | |||
You have gotten the admin account and password as the picture below by using command line. | |||
cat /etc/home/lphanvan/public_html/config.php | |||
[[File:Pass.png]] | |||
Figure 2: See the content of config.php " cat /etc/home/lphanvan/public_html/config.php " | |||
Now, let's login to database of website | |||
[[File:Dtb.png]] | |||
Figure 3: Login to database via shell | |||
=How to avoid Local Attack?= | |||
In my opinions, Local attack is one of dangerous attacking methods I have used so far. Below are my experiences to avoid the Local attack: | |||
- | - Should not use the source code when we do not know where it comes from, malicious code might be attached. | ||
- | - Checking the update of source codes as well as server to fix vulnerability frequently. | ||
- | - Change the password to be stronger and hard to brute force. | ||
- Set chmod 400 for sensitive files and 101 for folders. | |||
- Use VPS instead of using host to avoid local attack. | |||
- Data back up and scan the data to realize it's having malicious code or not. | |||
These are my experiences to avoid Local Attack. Surely, It might not a perfect way to avoid, but at least it could help us to reduce the risk. | |||
=References= | |||
'''English Websites''' | |||
''http://linuxcommand.org/lts0010.php'' | |||
''http://linuxcommand.org/learning_the_shell.php'' | |||
''http://linuxcommand.org/lts0070.php'' | |||
'''Vietnamese Websites''' | |||
''http://kechocgian.blogspot.com.ee/2013/08/huong-dan-tong-hop-chi-tiet-co-ban-nhat.html'' | |||
''http://namcoder.com/hack-local-attack-va-cach-phong-tranh/'' | |||
''http://duyk.net/topic/20-Huong-dan-local-attack-voi-mot-so-phuong-phap-co-ban'' | |||
'''Video''' | |||
''https://www.youtube.com/watch?v=RcusKpvKR_w'' | |||
=See more= | |||
You might want to see more: | |||
'''https://www.youtube.com/watch?v=FjgKtBAiLKQ''' | |||
'''https://www.youtube.com/watch?v=6hJ-d2NYLBg''' | |||
''' | '''https://www.youtube.com/watch?v=HpY6JxIzs1g''' | ||
= | =Conclusion= | ||
As what I wrote above are an outline of the Local Attack method which attackers can use their php shell to exploit not even one website it could be all of websites are standing in a same server. In which the attack can execute the command line to your server to find out the password of your database or host. Get Root access is possible if the Linux server are not being updated. Those steps above might not be used successfully in some cases, because it depends on the configuration of administrator and the version of server is setting up. | |||
=Contact= | =Contact= | ||
| Line 283: | Line 306: | ||
[['''''!!! This article is served for education purpose only, I will not responsibility for any harm made by other ones !!!''''']] | [['''''!!! This article is served for education purpose only, I will not responsibility for any harm made by other ones !!!''''']] | ||
[[Category:Operatsioonisüsteemide administreerimine ja sidumine]] | |||
Latest revision as of 00:43, 30 January 2017
Abstract
This article will be concerned about one of the common hacking methods in recent decades or even nowadays it is still being used by attackers. Its named Local Attack, this name is not the international official name for it. It was called by many Vietnamese Hackers, by somehow I realized it's quite good to describe partly of this attack method, so I'd like to take this name to be " our speaking" at least in this article. "This name is not available in google if you type by English "
I will illustrate the definition of Local Attack as well as the difficulties we will be suffered when we apply it beside its powerful. I will be talking detail step by step belongs with the certain knowledge what we need to know basically to do much straightforwardly and more understand its purpose. The knowledge requirement will be not hard to stop you getting the most powerful of hacking such as Web App, Linux command lines, Networking, etc.
Because of the security of our website and server, I will not show the php shell link in this article. I apologize for this inconvenient.
Keywords : Hacking, Local attack ,Linux , Web App.
Local Attack Introduction
What is Local Attack?
In generally, once we host the website to server, after that the user will be provided an " user account" and the directory/folder to mange their website. For instance, the first user has a website "A" and one directory/folder : /home/user1 to manage first user Similarly, the second user has a website "B" and one directory/folder /home/user2 to manage.
Local attack is the method which is applied to hack a website in the same server. For example, I want to attack website "A" from user 1, but unfortunately I could not find out the vulnerabilities to exploit and get an lien from it that means I have no way to attack based on this site "A". So, I will look for the websites which are being on the same server with "A", could be website "B" or "C".
Based on site "B" or "C" both of them are getting some vulnerabilities or another words is " hackable ". After getting the authorities on these site "B" or "C", I will upload the php file named " Shell " to the server of "B" or "C" it's also the server of website "A". The hacking process is starting from now.....
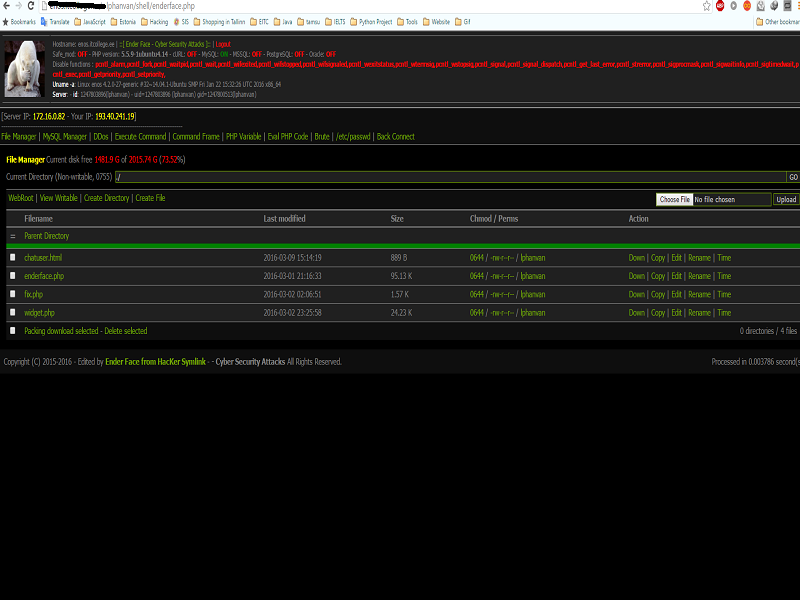 Firgure 1: Php shell was uploaded to host of the website.
Firgure 1: Php shell was uploaded to host of the website.
Pros and Cons of Local Attack
Pros:
*Does not take a lot of time.
*Easy to interact with the server via shell and exploit it.
Cons:
*Leave the " mark ", The administrator would be able to find where the shell comes from.
*If the websites are using separate server, Local Attack will be gotten some certain difficult.
What we need to know?
Host and Shared-Host
Normally for web site, its data must be stored on one server (server) is always active and connected to the internet. Storage space on the server used to store the data of the website is called the host. For a number of agencies and organizations, the hired one server for data storage is not practical website. Due to their needs is simply stored, further 1 server rental price is not cheap. Therefore, shared hosting is a reasonable choice. With shared hosting, server memory space is divided into many small hosts, and are separate from each rental. So on one server will contain data for multiple websites, and there is also a source of security for developing local attack.
Operating System and Decentralized system
The Operating system of the server must be Linux
Unlike Windows, Linux operating system has a decentralized system is complicated and strict. Linux supports three permissions to do with files :
r: read access (read)
w: right to record (write)
x: right to execute (execute)
-: not allowed
These rights are assigned to three subjects:
u: owner (owner)
g: group ownership (group)
o: the ordinary users (other)
You can read more here: http://linuxcommand.org/lts0070.php
Shell
Simply put, the shell is a program that takes your commands from the keyboard and gives them to the operating system to perform. In the old days, it was the only user interface available on a Unix computer. Nowadays, we have graphical user interfaces (GUIs) in addition to command line interfaces (CLIs) such as the shell.
On most Linux systems a program called bash (which stands for Bourne Again SHell, an enhanced version of the original Bourne shell program, sh, written by Steve Bourne) acts as the shell program. There are several additional shell programs available on a typical Linux system. These include: ksh, tcsh and zsh.
In this tutorial, I will use the shell php named: Shell r57 or c99. You can download it on google
See more here:
-http://linuxcommand.org/lts0010.php
-http://linuxcommand.org/learning_the_shell.php
*I recommend you use those shells or download it in virtual machines .
How to do Local attack step by step ?
1. View the list of user in server
2. Find the config.php file
3. Get the login information to database
4. Crack and change the password of admin
5. Login and upload the shell
View the list of user in server
If we want to local attack a website as I mentioned before, we need to know the users on the server and which sources it is? . After that , we have able to read the config.php file of the user
The command line to get the user:
cat /etc/passwd
Some cases, If the above command line does not show the user list, we could try this:
ls -l /home/
If the server ban to cat the passwd, use could use these command lines:
less /etc/passwd ./cat/etc/passwd
Find the path file config.php
Depending on the sources the path file will set be default like this: Note: Path is the path locates from server to the site
-With linux:
/home/user/public_html
Or other
-Joomla:
path/configuration.php
-Word-Press:
path/wp-config.php
This is the default path of those type of servers it's being used. It might be changed depended on Administrators (This is mainly due to the habits of programmers ).
(To search for the source path, search by keywords: "cwd", we will see similar code: "require_once (CWD. '/includes/init.php');" - This is the path defaults resulting init.php file)) ......
Get the information from config file
This is the most difficult step of the method
The basic command lines using for Local Attack
-ls, dir: List the names of the files inside the folder ls -al, ls -lia: List the names and attributes of files inside the folder
ls -lia "/home/lphanvan/public_html/@ender/includes.config.php"
-sand, ./cat, less, more, tail: View contents inside the file:
cat "/home/lphanvan/public_html/@ender/includes/config.php"
-ln: Command symbolic link:
ln -s "/home/lphanvan/public_html/@ender/includes/config.php%20ender.ini"
-cd: Convert directory
For example, to navigate to the folder
cd / home / lphanvan/ public_html / @ender/ includes / itcollege
cd ~: Go to Facebook's home directory
-chmod: Distribution rights for files or folders:
chmod 400 config.php (working in the directory where the file includes config.php)
-mkdir: create directory:
For me, I want to create a folder in the directory includes:
mkdir / home / lphanvan/ public_html / @ ender/ includes / itcollege
-touch: Create file:
touch /home/lphanvan/public_html/@ender/includes/itcollege.php
-tar, tip: compress and uncompress command: often used in root symlink
tar -zcvf enderhacked.tar.gz soleil (Compressed file folder enderhacked.tar.gz ender)
tar -zxvf enderhacked.tar.gz (unzip files enderhacked.tar.gz)
See more here: http://linuxcommand.org/lts0070.php
Some techniques to get useful information from config.php
1-Using the cat command, dim to see the folder name, file and read the file contents.
Example: dir / home / lphanvan/ public_html / includes
cat /homme/lphanvan/public_html/includes/config.php
But now the majority of servers are not allowed to exercise this function should apply this method will not work,
2-Using Symbolic links - Referred to as symlink
Symbolic links are basic techniques, and almost as important that the majority of the first attaker think before doing work local attack.
ln -s "/ home / lphanvan/ public_html / @ ender/ includes /config.php% itcollege.ini "
It can be understood simply create one file on the host itcollege.ini with identical content lphanvan config.php file on the server with the user's path
"/home/lphanvan/public_html/@ender/includes/config.php"
You can read more detail here: http://linuxcommand.org/learning_the_shell.php
Cracking and Changing the admin's password !!!!
In this case the admin's password does not be encoded by hash, so you do not need to crack it. In many cases, the content would not be showed and the password will be in hash.
You have gotten the admin account and password as the picture below by using command line.
cat /etc/home/lphanvan/public_html/config.php
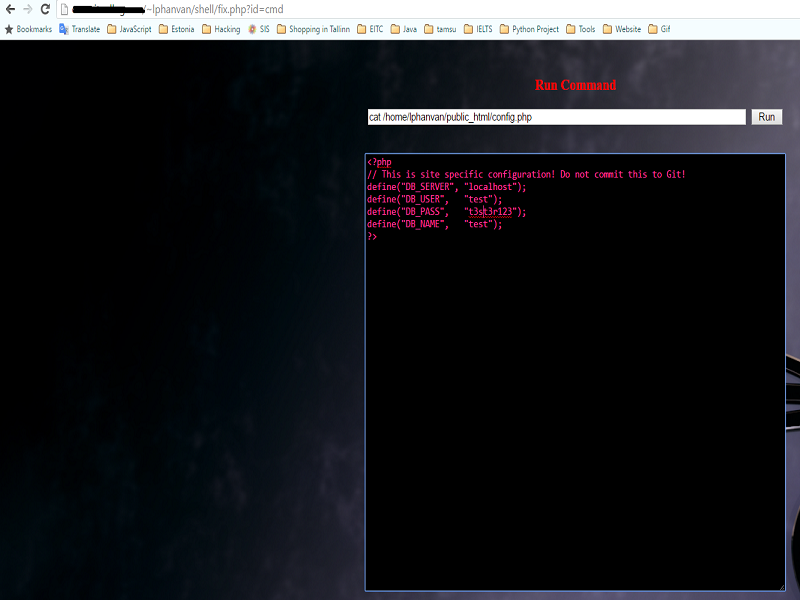 Figure 2: See the content of config.php " cat /etc/home/lphanvan/public_html/config.php "
Figure 2: See the content of config.php " cat /etc/home/lphanvan/public_html/config.php "
Now, let's login to database of website
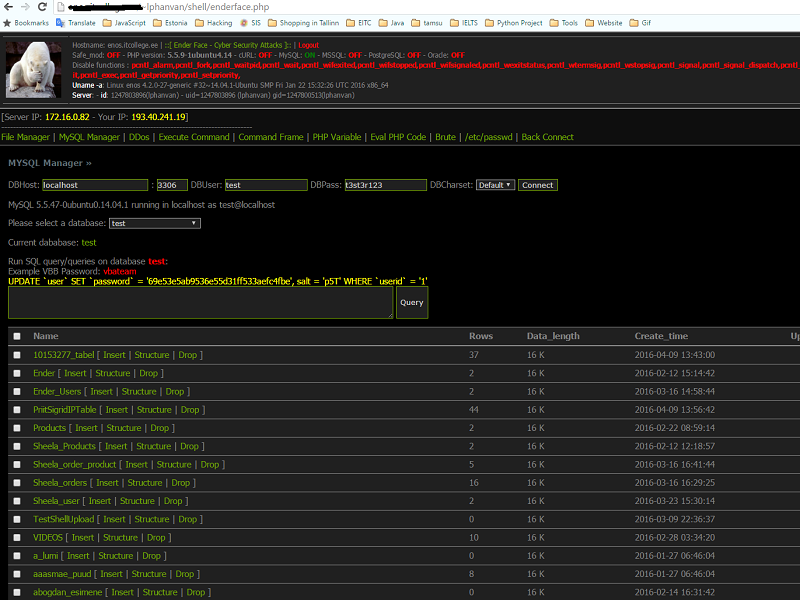 Figure 3: Login to database via shell
Figure 3: Login to database via shell
How to avoid Local Attack?
In my opinions, Local attack is one of dangerous attacking methods I have used so far. Below are my experiences to avoid the Local attack:
- Should not use the source code when we do not know where it comes from, malicious code might be attached.
- Checking the update of source codes as well as server to fix vulnerability frequently.
- Change the password to be stronger and hard to brute force.
- Set chmod 400 for sensitive files and 101 for folders.
- Use VPS instead of using host to avoid local attack.
- Data back up and scan the data to realize it's having malicious code or not.
These are my experiences to avoid Local Attack. Surely, It might not a perfect way to avoid, but at least it could help us to reduce the risk.
References
English Websites
http://linuxcommand.org/lts0010.php
http://linuxcommand.org/learning_the_shell.php
http://linuxcommand.org/lts0070.php
Vietnamese Websites
http://kechocgian.blogspot.com.ee/2013/08/huong-dan-tong-hop-chi-tiet-co-ban-nhat.html
http://namcoder.com/hack-local-attack-va-cach-phong-tranh/
http://duyk.net/topic/20-Huong-dan-local-attack-voi-mot-so-phuong-phap-co-ban
Video
https://www.youtube.com/watch?v=RcusKpvKR_w
See more
You might want to see more:
https://www.youtube.com/watch?v=FjgKtBAiLKQ
https://www.youtube.com/watch?v=6hJ-d2NYLBg
https://www.youtube.com/watch?v=HpY6JxIzs1g
Conclusion
As what I wrote above are an outline of the Local Attack method which attackers can use their php shell to exploit not even one website it could be all of websites are standing in a same server. In which the attack can execute the command line to your server to find out the password of your database or host. Get Root access is possible if the Linux server are not being updated. Those steps above might not be used successfully in some cases, because it depends on the configuration of administrator and the version of server is setting up.
Contact
If you want to know more about this method, please do not be hesitated to keep in touch with me :D
Ender Phan- Cyber Security Engineering- C11
The Estonian Information Technology College
Email: lphanvan@itcollege.ee
My site: cybercoffee.xyz